It’s getting harder than ever for businesses to keep their data safe.
Between remote work, cloud services, and third-party integrations, sensitive information now moves faster and across more touchpoints than traditional security models were built to handle.
Luckily, there’s a new generation of data loss prevention tools on the market. Ones that boast advanced features and leverage AI to resolve data security incidents.
To help you decide between them, we’ve put together a list of the very best data loss prevention solutions available right now. Scroll down for more, or use the menu to skip to a provider.
What Are the Best DLP Solutions in 2026?
| Tool | Description | Best For |
|---|---|---|
| Teramind | Behavioral DLP solution with real-time user activity monitoring (UAM) and AI-driven analytics. | Organizations needing comprehensive behavioral analysis and insider threat protection. |
| Mimecast Incydr | SaaS solution focused on insider risk detection and threat management. | Enterprises facing risks of data exposure and exfiltration by insiders. |
| Trend Micro iDLP | Integrated DLP that simplifies security by connecting with existing Trend Micro systems. | Low-cost buyers seeking quick implementation. |
| Symantec DLP | Modular enterprise data security solution with deep inspection capabilities. | Large enterprises with complex data protection needs. |
| Fortra (Digital Guardian) | Cloud-based endpoint DLP with comprehensive monitoring capabilities. | Organizations requiring military-grade data protection. |
| Trellix | Real-time data tracking and detection solution (formerly McAfee/FireEye). | Businesses needing advanced threat detection and response. |
| Forcepoint DLP | Enterprise-class DLP with global policy management and unified reporting. | Large organizations with diverse data protection requirements. |
| Proofpoint DLP | Email-focused DLP solution with strong machine learning capabilities. | Companies prioritizing email security and compliance. |
| Microsoft Purview DLP | Integrated DLP solution natively built into Microsoft 365 services. | Organizations heavily invested in the Microsoft ecosystem. |
| DTEX | Insider risk management and behavioral DLP solution. | Companies focusing on user behavior analytics and insider threats. |
| Cyberhaven | A Data Detection and Response (DDR) platform that uses proprietary data lineage technology. | High-growth, AI-driven environments needing to protect intellectual property. |
| Netwrix Endpoint Protector | A multi-OS endpoint DLP solution providing real-time protection for Windows, macOS, and Linux. | Highly regulated industries requiring strict peripheral device control and cross-platform compliance. |
| Zscaler | A cloud-native platform providing inline traffic inspection and AI-powered data discovery. | Large enterprises seeking to secure web and SaaS traffic for distributed workforces. |
| Netskope | A cloud-native SASE platform that uses machine learning classifiers and contextual risk awareness to secure data. | Organizations prioritizing adaptive data protection and secure Generative AI usage. |
1. Teramind
Find out how Teramind protected Arrivia’s data from insider theft — watch our video for the full story.
Teramind is a leading data loss prevention (DLP) and insider risk management platform. It’s designed for enterprises that need complete visibility into how their data is used, accessed, and moved across their organization.
The platform combines data loss prevention and behavior analytics into one unified solution. Once installed, it continuously tracks user actions across endpoints, applications, and networks to detect risky behavior.
Here’s an example of Teramind’s DLP engine in action:
Let’s say an employee in your firm copies restricted files to a USB storage device. Or uploads confidential data to an unauthorized cloud platform. Or shares sensitive documents via email.
When this happens, Teramind can:
- Automatically block those actions to stop the data from being stolen.
- Send warning alerts to your security department, speeding up incident response times.
- Provide forensic evidence of the breach in the form of activity logs, screen recordings, and file access histories.
What Are Teramind’s Key Features?
See Teramind’s DLP features in action → Take a free interactive product tour
- Context-Aware Behavioral Analytics: Teramind’s platform distinguishes between legitimate workflows and suspicious activity, such as unusual access sequences or unauthorized data transfers. It dramatically reduces false positives.
- Real-Time Intervention and Guidance: With Teramind, you can configure thresholds for automated responses, ranging from simple notifications to session termination. It prevents breaches before they occur, instead of just detecting them after the fact.
- Multi-Channel Endpoint Monitoring: Provides visibility across all exfiltration vectors, including file operations, clipboard activity, web uploads, and email attachments. Teramind protects sensitive data regardless of whether a user is working in a cloud app, a local document, or a messaging platform.
- Advanced Content Analysis: Sophisticated content inspection that uses Optical Character Recognition (OCR) to scan text in images and non-searchable files. With Teramind, no user can evade detection by taking screenshots or embedding data in images.
- Forensic-Ready Incident Response: Teramind supplies tamper-proof activity logs, detailed user timelines, and high-definition screen recordings of all user actions. It delivers court-admissible evidence that enables security teams to reconstruct incidents and speed up investigations.
- AI-Powered Intelligence Feed (OMNI): Teramind’s AI-driven alert system that groups data-related events into a “news feed” style dashboard. It highlights high-level trends and critical threats, allowing teams to act on insights rather than sifting through thousands of individual logs.
- Role-Based Access and Policy Control: Teramind offers granular security policies that can be customized for departments, roles, or individuals. It enforces “least-privilege” access without disrupting legitimate business tasks. You can apply strict rules for high-risk users while maintaining a lighter touch for trusted roles.
What Are Teramind’s Key Use Cases?
- Insider Threat Detection: Organizations can use Teramind to monitor user activities in real time, detecting anomalies such as unauthorized file transfers or unusual access to sensitive data.
- Endpoint Data Protection: Companies can deploy Teramind on employee devices to prevent confidential files (like customer lists or IP) from being copied to USB drives or sent via personal emails.
- Compliance Monitoring: Highly regulated sectors (finance, healthcare) can rely on Teramind’s behavior analytics and policy enforcement to ensure GDPR, HIPAA, or PCI DSS compliance.
Why Do Customers Trust Teramind as Their Data Security Solution?
- Proactive Data Leakage Prevention: Teramind’s user behavior monitoring features detect abnormal activity in real-time, allowing organizations to prevent potential data breaches before they occur. See G2 Review →
- Secure Sensitive Data Handling: The platform provides robust protection for sensitive client information, ensuring that data is managed securely and meets high privacy standards. See G2 Review →
- Privacy-Conscious Productivity Tracking: The platform provides deep visibility into workflow metrics without compromising employee privacy, ensuring a secure and comfortable work environment. See G2 Review →
- Exceptional Customer Support: Users benefit from a long-standing, reliable solution backed by a support team that is widely considered second to none. See G2 Review →
What is Teramind’s Pricing?
Here’s a breakdown of Teramind’s pricing tiers (based on 5 seats, billed annually):
- Starter ($14/seat/month): Best for basic productivity use cases and identifying risky users. Includes quick visual evidence capture, live playback, and website/app tracking.
- UAM ($28/seat/month): Designed for comprehensive productivity optimization and security detection. This tier includes everything in Starter plus full digital activity telemetry, UEBA (User and Entity Behavior Analytics), forensics, and unlimited behavior rules.
- DLP ($32/seat/month): Best for comprehensive intent-based security detection and response. It includes everything in UAM plus content-based data exfiltration prevention and automated actions to block data leaks in real-time.
- Enterprise (Custom pricing): Tailored professional services for the most demanding large-scale enterprises and government organizations. Includes everything in DLP plus in-app parsing for fraud detection, an OCR engine, and unlimited activity-based behavior rules.
All paid plans shown above reflect an 8% discount for annual billing compared to the monthly rates.
See Teramind’s capabilities before committing → Click here for a live demo
2. Mimecast Incydr (formerly Code42 Incydr)
See how Teramind compares to Mimecast Incydr →
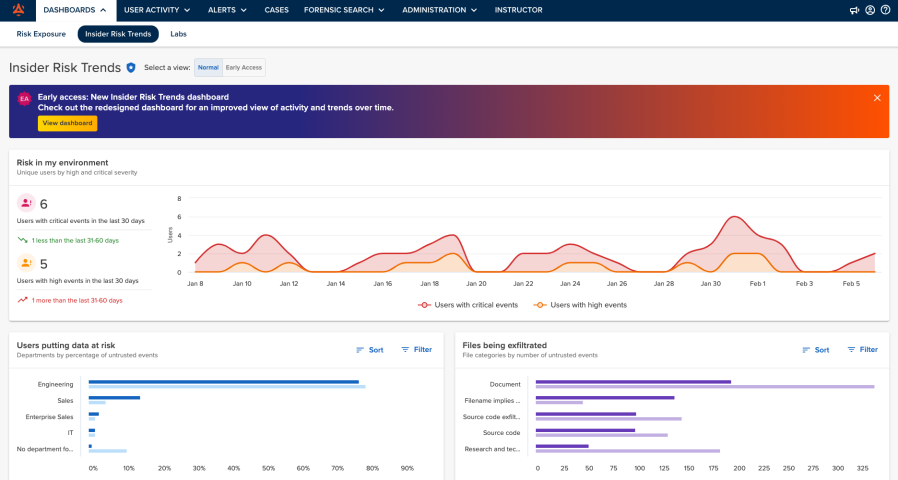
Mimecast Incydr is a cloud-native data protection and insider risk management platform that helps organizations stop data loss or theft. It does this by emphasizing context and behaviour — i.e., who is moving the data, where it’s going, and how this compares to expectations.
The engine behind this approach is the PRISM (Proactive Risk Identification & Severity Model). It uses over 250 risk indicators: data context (e.g., file sensitivity, location), user context (e.g., role, history, behavior), and destination context (e.g., upload location, cloud service). It then scores and prioritizes events so that the most critical incidents surface quickly.
Mimecast Incydr also supports automated remediation workflows such as blocking uploads, revoking permissions, and launching training modules to users who trigger risky actions.
Key Features
- Watchlists and Targeted High-Risk User Controls: Users can create “watchlists”, i.e., groups of users who warrant elevated monitoring (e.g., contractors, departing employees, senior IP-holders). They can also apply controls (blocking, tighter monitoring) to those groups.
- Exfiltration Controls: Incydr monitors browser uploads, clipboard-paste actions, and unsanctioned cloud app usage.
- Micro-Training: When Incydr detects a risky behavior, it automatically triggers responses such as blocking the action, sending tailored micro-training to the user, quarantining the file, or escalating to a case in the SOC workflow.
Use Cases
- Employee Offboarding Risk Management: Before or during employee exits, Incydr can track data access and transfers to ensure no confidential files leave the organization.
- Cloud Collaboration Oversight: Companies can use it to monitor data sharing across Google Drive, Slack, or Microsoft 365, helping them to spot unsafe behaviors in real time.
Pricing
Contact Mimecast’s sales team for pricing options.
3. Trend Micro iDLP
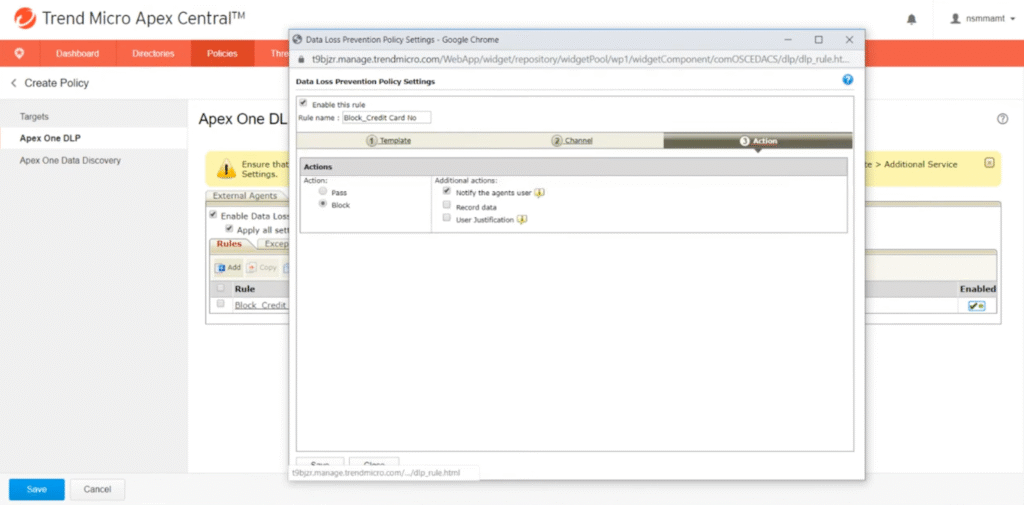
Trend Micro’s iDLP offering is designed to give enterprises a lightweight yet integrated option for data loss prevention. It’s good if you want to extend DLP controls across endpoints, networks, and cloud without deploying a completely separate infrastructure.
The solution is built to protect sensitive and proprietary data in motion (via USB drives, email, cloud uploads), in use (copy, print, screenshot on endpoint), and at rest (file shares, archives) while leveraging the broader Trend Micro security ecosystem — the company’s Apex One endpoint agent or OfficeScan Data Protection Service.
Key Features
- Granular Device Control: Users can set rules based on removable device vendor and serial number (USB drives, CD/DVD writers, other media). This enables blocking or restricting specific devices rather than all removable media.
- Pre-Built Compliance Templates: Comes with out-of-the-box templates (PCI DSS, HIPAA, GLBA, US PII, etc.), plus international data-identifier patterns you can extend or customize.
- Centralised Management via Trend Micro Control Manager: Policies, events, reporting, and configuration across the iDLP modules and other Trend Micro products are unified under one console.
Use Cases
- Industry-Specific Data Protection: Financial institutions can use iDLP to detect exposure of SWIFT codes, credit card numbers, and IBANs. Healthcare providers can also use it to configure policies to protect PHI under HIPAA.
- Securing Data During Cloud Migration: During digital transformation, sensitive workloads often move from on-prem servers to cloud environments. iDLP helps by inspecting and classifying files during migration, ensuring no private data is exposed or uploaded to non-compliant repositories.
Pricing
Visit Trend Micro’s website to request a quote.
4. Symantec DLP
See how Teramind compares to Symantec DLP →
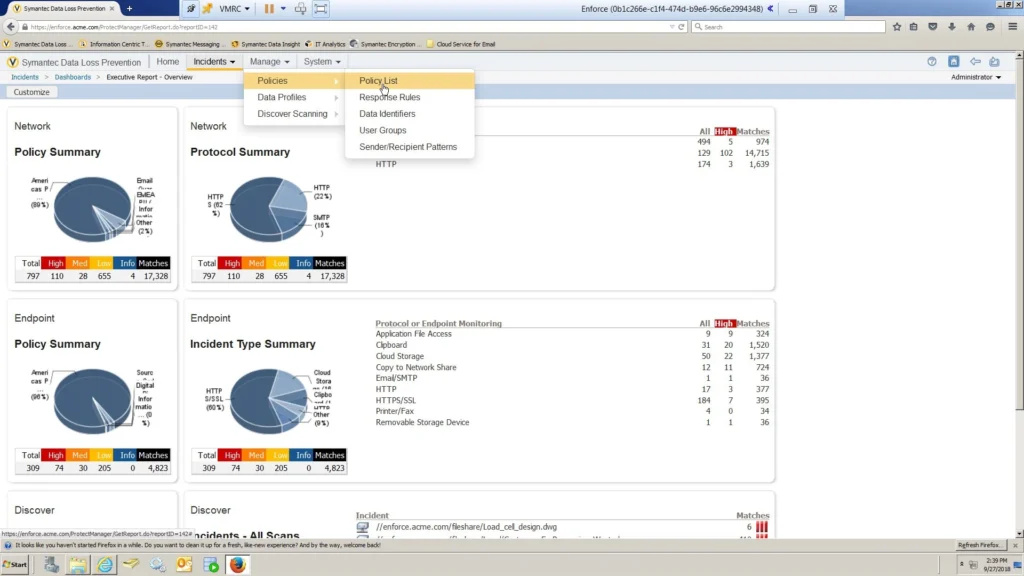
Symantec Data Loss Prevention (now part of Broadcom Inc’s cybersecurity portfolio) is another solution that gives organizations full visibility and control over sensitive data across their endpoints, networks, storage, and cloud environments.
It offers a unified console and policy framework. With this, security teams can define rules and workflows that apply across endpoints, network, cloud, and storage.
There are also advanced detection capabilities, such as content inspection, pattern matching (regex), fingerprinting, OCR, and contextual analysis of user behavior and data movement.
Key Features
- EDM (Exact Data Matching): Symantec can fingerprint an exact dataset (e.g., a database of customer records) and then monitor those exact values in motion, at rest, or in use.
- IDM (Indexed Document Matching): This is used to index large volumes of documents (such as engineering drawings, contracts, IP-documents) and then detect if those documents (or portions of them) appear in places they shouldn’t.
- ICA (Information-Centric Analytics): This module uses analytics and user/entity behaviour context to help prioritise risky events and reduce false positives.
- Offline and Remote Device Coverage: For devices that are off-network or remote, the endpoint agent continues to enforce policies, monitor data in use (USB, copy/paste, print), and block high-risk actions.
Use Cases
- Enterprise-Wide Policy Enforcement: Global enterprises can use Symantec DLP to define and enforce data protection policies across endpoints, servers, and networks.
- Data Protection in Complex Hybrid Clouds: Symantec DLP integrates with cloud APIs and network monitors, maintaining visibility and control over data regardless of storage location.
Pricing
Contact Broadcom to see Symantec DLP’s pricing options.
5. Fortra DLP (formerly Digital Guardian)
See how Teramind compares to Fortra →
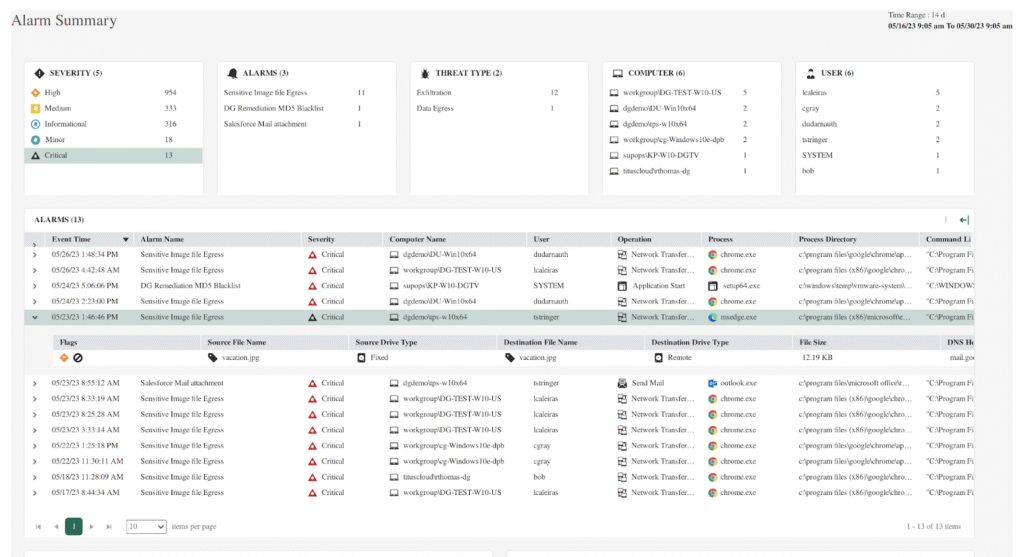
Fortra DLP is a SaaS solution that focuses on granular control of sensitive data at the endpoint level. It covers laptops, desktops, and other devices where data is created, used, moved, or stored on- or off-network.
The platform deploys a lightweight endpoint agent that monitors data (in use, at rest, and in motion). It then records detailed metadata about every data event, including file creation, copying, uploads, print operations, and removable-media activity.
Plus, since it operates close to the OS level, it can capture fine-grained details about what users do, the applications involved, and where the data goes.
Key Features
- Adaptive Data Protection Policies: The solution applies protection based on risk levels, user roles, and business context. For example, a policy might allow engineers to transfer CAD files within an internal domain but automatically encrypt or block the same files if transferred externally.
- Centralized Management Console: All endpoint agents feed into a unified management console, where administrators can define policies, monitor incidents, and generate compliance reports.
- Granular Endpoint Controls: This gives administrators full control over how users interact with data. It can block file transfers to USBs, restrict print operations, limit uploads to unsanctioned cloud apps, and enforce encryption for specific file categories.
Use Cases
- Intellectual Property and Design File Protection: R&D-heavy firms (like semiconductor or automotive companies) can use Fortra to identify, tag, and restrict access to sensitive file types such as CAD drawings, design specs, and formulas.
- Managed DLP-as-a-Service for Resource-Limited Teams: Fortra offers a managed DLP model that continuously tunes policies based on observed data flows. This can help smaller security teams maintain enterprise-grade protection without the operational overhead.
Pricing
Fill out a form on Fortra’s website to get a customized quote.
6. Trellix DLP
See how Teramind compares to Trellix →
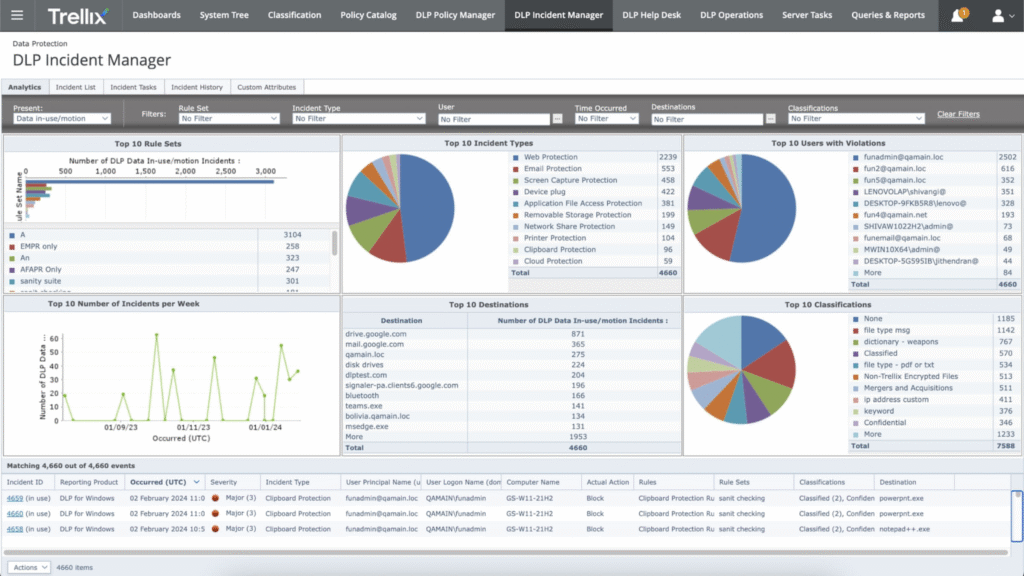
Trellix DLP is an enterprise data protection platform that detects, classifies, and secures sensitive data at every stage of its lifecycle. It combines data fingerprinting, machine learning classification, and policy-based controls to prevent unauthorized access or exfiltration.
It also integrates deeply with the company’s broader cybersecurity ecosystem, including Trellix EDR/XDR, ENS (Endpoint Security), and Trellix ePO (ePolicy Orchestrator) for centralized management. This enables organizations to unify data protection, endpoint defense, and threat detection into one adaptive framework.
Key Features
- Device Control: Trellix restricts removable media use, Bluetooth transfers, and other risky vectors that might enable data exfiltration.
- ePolicy Orchestrator (ePO): Administrators can define, deploy, and manage DLP policies across endpoints, networks, cloud apps, and email gateways from a single console.
- Cloud and Web Integration: Trellix DLP extends protection into cloud environments through integrations with CASB solutions and APIs for services like Microsoft 365, Google Workspace, Box, and Salesforce. It ensures the same data policies apply whether data resides on-premises or in the cloud.
Use Cases
- Real-Time Risk Analytics: Trellix leverages ML to establish baselines of normal user activity and detect deviations. This can help detect insider misuse or compromised accounts attempting data theft.
- Anomaly Detection: Organizations can use Trellix DLP to restrict or encrypt data written to removable media, ensuring USB drives or external disks can’t be used for covert data transfers.
Pricing
Trellix’s pricing isn’t publicly disclosed. Request a demo on its website for more information.
7. Forcepoint DLP
See how Teramind compares to Forcepoint DLP →
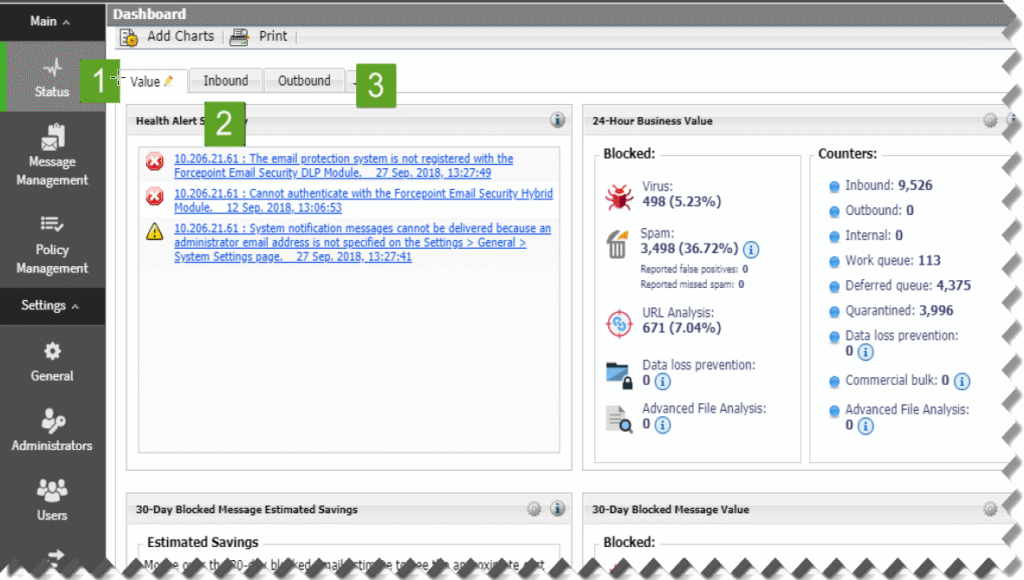
Forcepoint DLP is an enterprise security solution designed to prevent sensitive information from being accidentally exposed, maliciously stolen, or misused.
It combines content inspection, machine learning, and user behavior analytics (UBA) to identify and prevent data leaks across endpoints, networks, cloud apps, and email systems.
The platform is built on the Forcepoint ONE Security Service Edge (SSE), integrating with Forcepoint CASB, SWG, and ZTNA modules. This provides a unified platform to secure data wherever users work (office, at home, or in the cloud).
Key Features
- ContentIQ Engine: Offers a large base of over 1,700 classifiers and policy templates covering 80+ countries and 90+ regulations. Forcepoint supports hundreds of file types, NLP scripts, and image OCR detection.
- Risk-Adaptive Protection (RAP): Uses native analytics to evaluate user behavior, context, and data interaction patterns to dynamically adjust the risk level of users and actions.
- Advanced Data Discovery and Forensics: Enables organizations to scan storage repositories (on-premises and cloud) to locate sensitive data, tag owners, and create audit trails.
Use Cases
- Responsive Risk Analysis: If a user’s risk score rises due to unusual activity, Forcepoint can automatically increase restrictions, such as disabling data transfers or encrypting sessions.
- Intent-Based Adaptive DLP: Forcepoint can differentiate between different user intents — e.g., a legitimate file share and a malicious attempt to leak data. This can help organizations respond with adaptive policies like warning pop-ups for accidental violations or automatic blocking for risky behaviors.
Pricing
Visit Forcepoint’s website to request pricing information.
8. Proofpoint DLP
See how Teramind compares to Proofpoint →
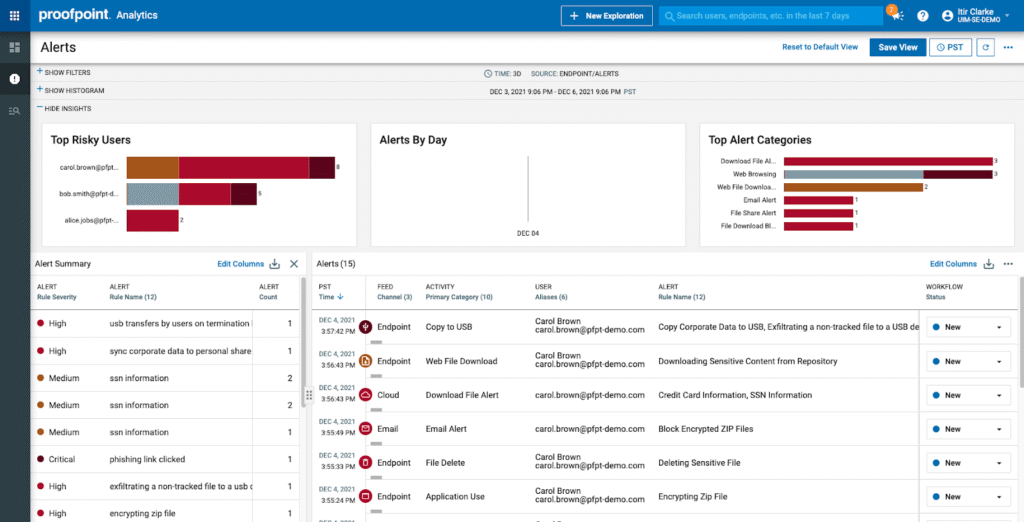
Proofpoint DLP positions itself as a ‘people-centric,’ cloud-native solution for protecting cloud applications, endpoints, emails, and on-premises repositories. The vendor combines user behavior telemetry and threat intelligence to understand how people interact with data in a network.
The idea is to adopt adaptive controls that reflect how people actually use and share information. In this case, monitoring file and data movements (uploads, downloads, email attachments, cloud shares), while correlating those actions with user context (role, behaviour, device) and threat context (compromised account, phishing event).
For example, Proofpoint’s email DLP component scans outbound email messages and attachments for regulated data patterns, custom dictionaries, or company-specific identifiers.
Key Features
- Rich Detector Library: Proofpoint provides extensive pre-built detectors (smart identifiers, regex, fingerprinting, OCR) and classification engines, plus support for custom dictionaries.
- Insider Threat Management (ITM): Provides visibility into user intent through session recording, behavioral baselining, and forensics, helping teams distinguish between mistakes and malicious acts.
- Audit-Ready Reporting: Detailed audit logs, incident snapshots, and activity playback allow analysts to reconstruct how data left the organization and demonstrate compliance during audits. Reports can be customized for regulations like the GDPR, CCPA, or industry frameworks such as ISO 27001.
Use Cases
- Email Data Breach Prevention: Protects outbound email communications by scanning attachments and message bodies for sensitive or regulated content.
- Integrated Insider Risk Program: With Proofpoint’s people-centric approach, security teams can identify users with high data movement tendencies, with the goal of delivering targeted training or enforcing stricter controls for those segments.
Pricing
Visit Proofpoint’s website to request a quote.
9. Microsoft Purview DLP
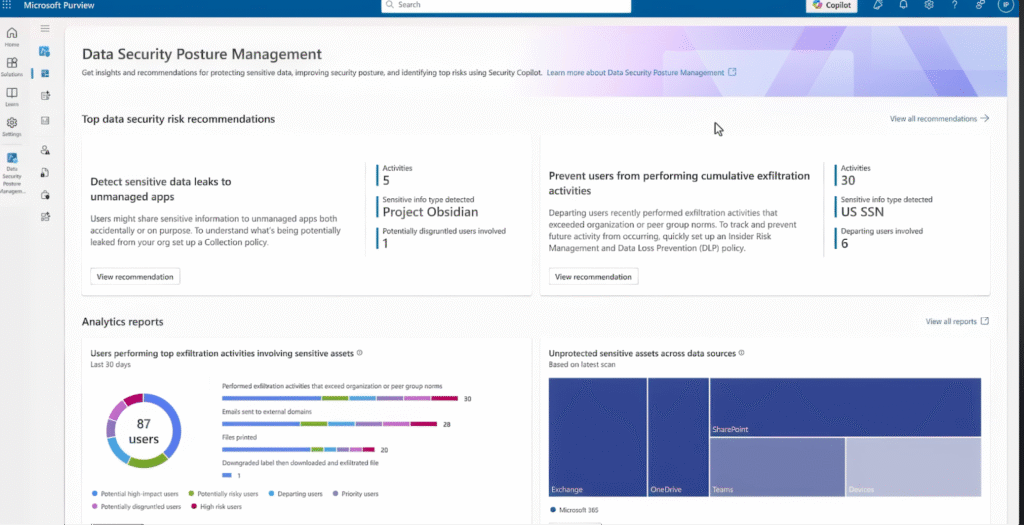
Microsoft Purview DLP is a unified, cloud-native data protection solution built into the Microsoft 365 ecosystem and extended across endpoints, on-premises repositories, and third-party cloud environments.
It’s designed to identify, monitor, and automatically protect sensitive data within Office apps, email, Teams, SharePoint, OneDrive, and even non-Microsoft services via connectors.
Purview DLP leverages Microsoft’s Information Protection framework, which combines data classification, sensitivity labeling, and policy-based controls.
When it detects sensitive content (like PII, financial data, or confidential business files), it applies the appropriate protection. This could be blocking sharing, encrypting data, restricting downloads, or simply warning users in real time.
Key Features
- Policy Tips: Because it’s part of Microsoft’s productivity stack, users receive policy tips directly within familiar interfaces like Outlook, Word, or Teams. This helps them make informed security decisions without disrupting workflow.
- Cloud App Governance and Endpoint DLP: Through Defender for Cloud Apps and Defender for Endpoint, Purview extends visibility to unmanaged devices and third-party cloud environments. Endpoint DLP monitors actions like copying data to USBs, printing, or uploading to personal drives. This ensures consistent protection even off-network.
- Automated Incident Response: When a violation occurs, Purview DLP logs detailed event metadata (user, file, action, sensitivity, location) and can automatically trigger incident workflows, alert administrators, or escalate to Microsoft Sentinel for SIEM correlation.
Use Cases
- Audit Automation: Purview helps compliance teams automatically generate reports demonstrating alignment with frameworks like the GDPR or ISO 27001.
- Cross-Cloud DLP Integration: Purview integrates with Windows Defender and third-party apps to prevent data leaks across devices and hybrid cloud systems.
Pricing
Visit the Microsoft website for up-to-date pricing information.
10. DTEX
See how Teramind compares to DTEX →
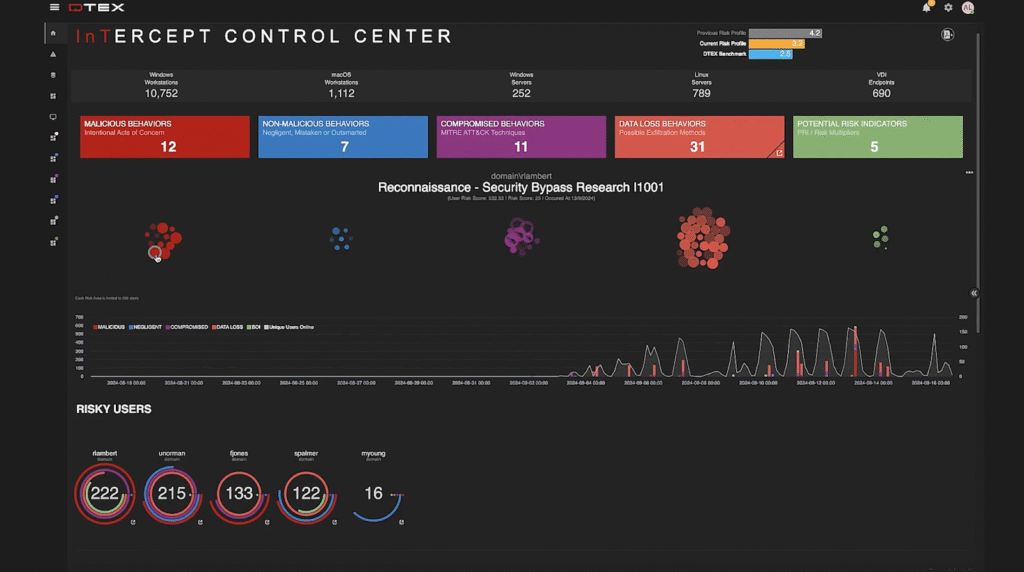
DTEX focuses on human behavior visibility, understanding why data is being moved or accessed before it ever leaves an environment.
The platform continuously collects anonymized endpoint telemetry at scale, covering user activity such as file creation, copying, network connections, process launches, and peripheral use.
Then it processes this data in real time through its DTEX InTERCEPT Behavioral Datalake, which applies advanced analytics and machine learning to identify risk patterns. This allows organizations to detect malicious insiders, compromised accounts, or negligent employees before data exfiltration occurs.
Key Features
- Timeline Reconstruction: InTERCEPT records complete user activity timelines, enabling security teams to reconstruct events leading to a policy violation or insider incident.
- Exfiltration Detection: The platform tracks all data interactions (including copy-paste, print, screenshot, USB transfer, and cloud uploads), correlating them with user behavior to detect anomalies that signal potential leaks or misuse.
- Intent Modeling: Uses predictive analytics to determine intent. If a user shows exfiltration signs, e.g., archiving large files or connecting unauthorized devices, the system escalates risk scores proactively.
Use Cases
- Pre-Exfiltration Detection: It continuously collects endpoint telemetry to profile normal user behavior, flagging deviations that signal insider risk or data misuse.
- Preserving Workforce Visibility: DTEX anonymizes behavioral data, allowing organizations to monitor and mitigate insider risks while maintaining employee privacy.
Pricing
Book a demo via DTEX’s website.
11. Cyberhaven
See this list of Cyberhaven alternatives →
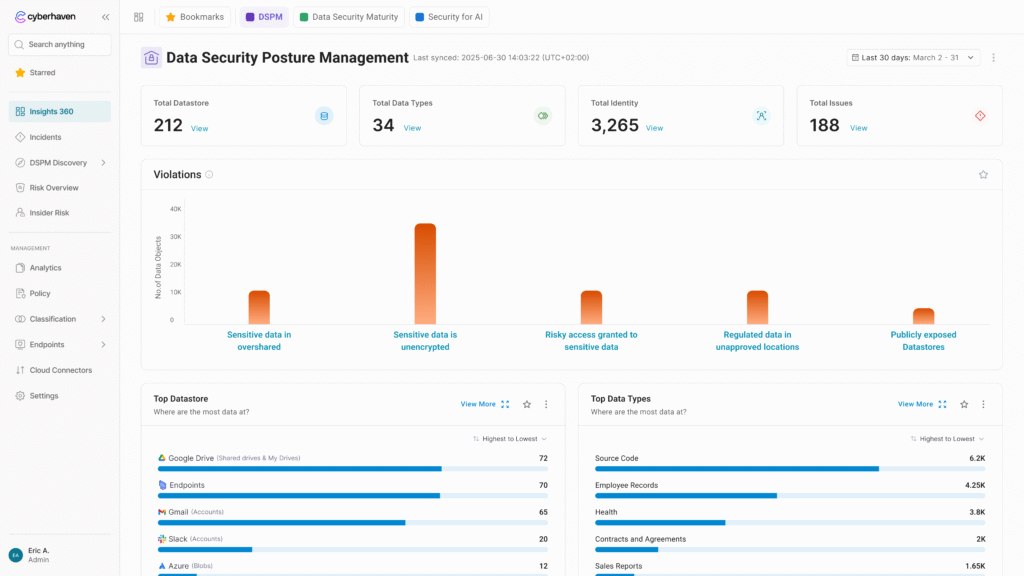
Cyberhaven focuses on data detection and response (DDR) and data security posture management (DSPM). It aims to protect data wherever it lives and moves across endpoints, cloud, SaaS, and AI tools.
The platform uses data lineage technology to continuously record every event for every piece of data — including moves, copies, edits, and shares — capturing the context that traditional content-scanning tools often miss.
By correlating this lineage with behavioral signals through its AI engine, Cyberhaven identifies risky activities in real time. It allows organizations to intervene immediately with automated remediation, such as blocking exfiltration or coaching users through contextual prompts, to prevent data loss before it happens.
Key Features
- Data Lineage Tracing: Automatically tracks the journey of data from its origin through every interaction, preserving context even when data is copied, pasted, or fragmented across different applications.
- Linea AI Engine: Employs advanced AI and machine learning to classify data semantically and detect anomalies, reducing false positives.
- Real-Time User Coaching: Provides just-in-time education to employees when risky behavior is detected. Cyberhaven offers optional overrides with justifications, maintaining productivity while reinforcing security policies.
Use Cases
- Comprehensive Exfiltration Prevention: Protects high-value data such as source code and client information from leaving through unauthorized channels like personal cloud storage, web uploads, or AI tools.
- Accelerated Incident Investigation: Simplifies forensic analysis by providing security teams with a complete record of data interactions and screen activity, helping them quickly determine intent and resolve threats.
Pricing
You must book a demo to see Cyberhaven’s pricing.
12. Netwrix Endpoint Protector
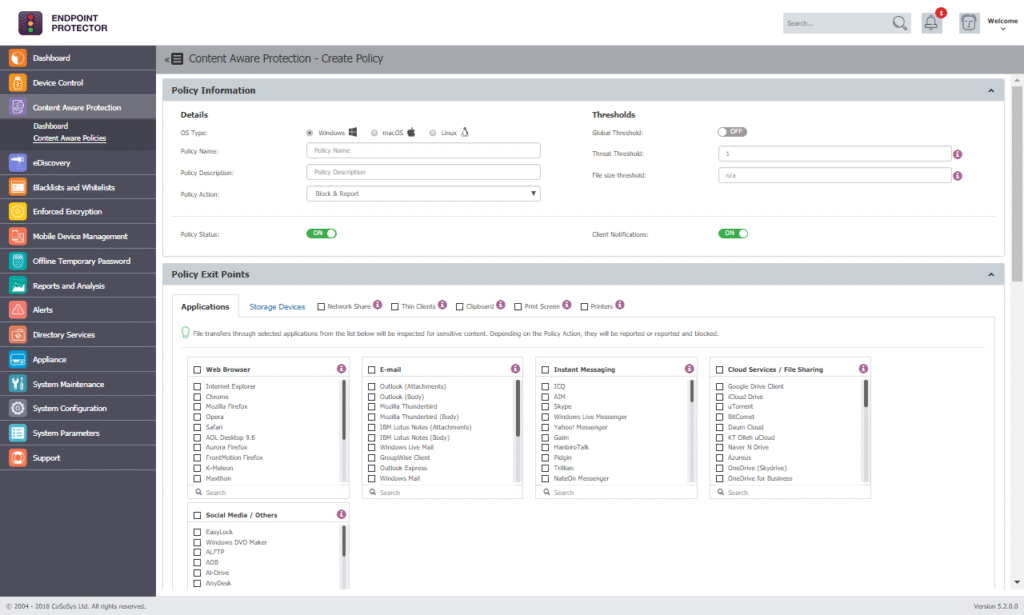
Netwrix Endpoint Protector focuses on multi-OS endpoint data loss prevention (DLP) and device control, aiming to secure sensitive data across Windows, macOS, and Linux. The solution is designed to prevent data theft and accidental leaks by controlling every major exit point on the endpoint.
The platform continuously monitors data interactions and transfers, capturing telemetry for file movements, clipboard activity, and interactions with peripheral devices like USBs. It employs advanced OCR technology to extract text from images and screenshots, ensuring visibility into data that traditional text-based tools might miss.
Processing this data in real time, the solution applies content-aware policies and behavioral analysis to detect suspicious activities such as unauthorized file transfers or ransomware signatures. This allows organizations to take immediate remediation actions — such as blocking transfers or encrypting files — even when devices are offline.
Key Features
- Granular Device Control: Provides detailed management of over 45 classes of peripheral devices, including USB drives, Bluetooth, and printers, allowing admins to set rights based on vendor or serial number.
- Enforced Encryption: Automatically secures data copied to authorized USB storage devices using FIPS-validated 256-bit AES encryption. This protects data if a device is lost or stolen.
- Content-Aware DLP: Contextually scans data in transit across applications, browsers, and messaging platforms, utilizing N-gram-based text categorization to identify sensitive intellectual property and source code.
Use Cases
- Regulatory Compliance: Helps organizations meet strict requirements for standards like CMMC, PCI DSS, and GDPR by securing PII and maintaining comprehensive audit trails for data movement.
- Insider Threat Prevention: Mitigates the risk of data theft by monitoring and blocking risky behaviors, such as unauthorized cloud uploads or copying data to unapproved removable media.
Pricing
Visit Netwrix’s website to request a personalized quote.
13. Zscaler
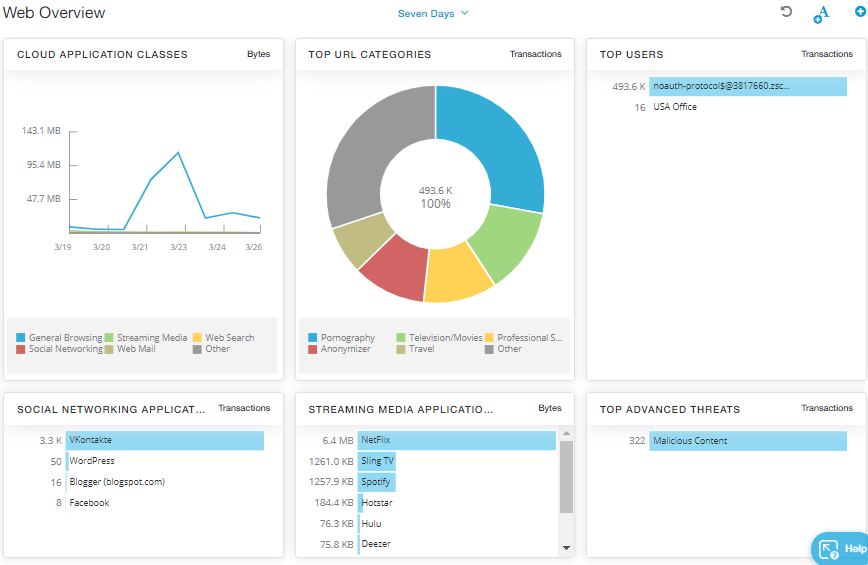
Zscaler focuses on cloud-native data loss prevention (DLP) integrated into its Zero Trust Exchange platform. By routing traffic through its global security cloud, Zscaler eliminates the need for on-premises hardware while providing identical protection for in-office and remote users.
The platform continuously collects data telemetry from internet-bound traffic and user devices, including web uploads, email attachments, and endpoint activities such as USB transfers and printing. It leverages AI-powered discovery to automatically find and classify sensitive data like PII, financial records, and intellectual property across distributed environments.
Processing every byte inline with full SSL inspection, Zscaler applies real-time policies to detect risky behaviors and exfiltration attempts. This enables immediate enforcement actions — such as blocking transfers, encrypting content, or coaching users through automated justifications — ensuring airtight protection regardless of a user’s connection status.
Key Features
- Advanced Data Classification: Uses Exact Data Matching (EDM) to fingerprint specific database records and Indexed Document Matching (IDM) to detect sensitive form templates.
- Optical Character Recognition (OCR): Scans and classifies text within image files (PNG, JPEG) and images embedded in documents, ensuring visual data is protected alongside plain text.
- Workflow Automation: Streamlines incident response by assigning violations to users for justification or routing them to security teams, helping employees learn safe data handling in the moment.
Use Cases
- Secure Generative AI Usage: Provides visibility into AI prompts and usage, blocking risky access and enforcing inline DLP to prevent sensitive data from being leaked to GenAI platforms.
- Unified Endpoint Protection: Secures device data from lateral movement and exfiltration via USB, network shares, or printing, particularly during high-risk scenarios like employee resignations.
Pricing
Zscaler offers two platform bundles with optional add-ons, although it gates the exact costs behind a form.
14. Netskope
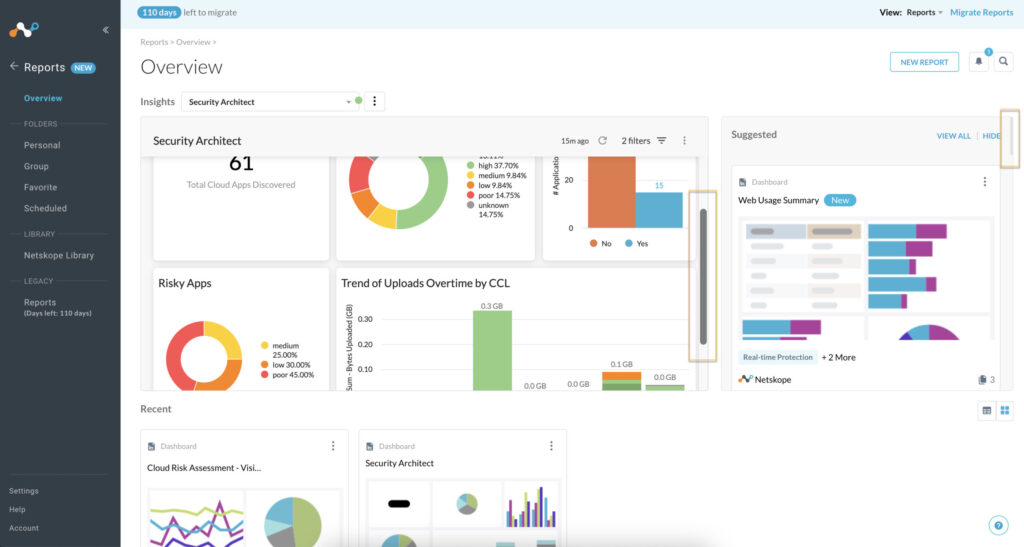
Netskope focuses on zero-trust data protection through its cloud-native Netskope One platform. It’s designed to adapt its security response based on changing user behaviors, organizational risk levels, and deep security context.
The platform continuously monitors data movement in-motion, at-rest, and in-use across the entire corporate environment, regardless of whether users are on-premises or remote. It collects extensive telemetry by inspecting traffic from browsers, mobile apps, and sync clients, even going beyond simple content analysis to examine metadata, hidden fields, and comments.
Using its patented Cloud XD engine and machine learning classifiers, Netskope identifies risky activities — such as sharing sensitive data with Generative AI or unauthorized cloud apps — in real time. This enables a closed-loop remediation workflow where organizations can instantly block, quarantine, or encrypt sensitive content while providing real-time coaching to warn end users about policy violations.
Key Features
- Advanced ML Classification: Employs over 3,000 data identifiers and 26+ machine learning classifiers to accurately detect sensitive items like patents, tax forms, and source code across thousands of file types.
- Contextual Risk Awareness: Factors in identity, device status (managed vs. unmanaged), location, and application risk to automatically adapt data protection policies.
- Optical Character Recognition (OCR): Extracts text from unstructured formats like images and screenshots — including whiteboard photos or driver licenses — to ensure sensitive information is identified even when it’s not in a traditional document.
Use Cases
- Secure AI Innovation: Monitors and controls data shared with generative AI tools like ChatGPT, preventing sensitive corporate information from being leaked into public machine learning models.
- Malicious Insider Detection: Identifies anomalous employee behavior and intentional exfiltration attempts, such as frequent USB copies or data transfers to personal email accounts.
Pricing
Pricing isn’t available on the Netskope site; you must fill out a form to get a quote.
FAQs
What Are DLP Solutions?
DLP solutions are platforms that help you identify, monitor, and protect sensitive data across endpoints, networks, cloud-based apps, and storage environments.
They give security teams the insight to understand where critical data lives, who has access to it, and how it’s being shared. This way, they can prevent accidental leaks, ransomware attacks, unauthorized access, malicious exfiltration, or other forms of cyber threats before they happen.
Beyond protecting intellectual property (IP) and customer data, DLP plays a critical role in meeting global compliance obligations like the GDPR, HIPAA, and PCI DSS.
What Does DLP Software Do?
DLP software, or Data Loss Prevention software, helps organizations protect sensitive data by monitoring, detecting, and preventing unauthorized access or data leaks.
It enables businesses to define policies, monitor user activity, and take immediate action to mitigate the risk of data breaches or loss.
What is an Example of DLP?
An example of DLP (Data Loss Prevention) software is Teramind DLP, which offers data identification and prevention capabilities, along with integrations with existing security infrastructure.
Teramind is a popular choice for organizations looking to secure sensitive data and ensure compliance with data protection regulations.
Why Do You Need DLP Tools?
Almost any type of company is at risk of damaging data loss.
In the last quarter of 2025 alone, we’ve seen several high-profile attacks make the headlines:
- Hackers stole 5.7 million customer records belonging to Qantas.
- The PII of approximately 70,000 Discord users was leaked.
- SonicWall announced a data exposure impacting 17,000 organizations using its cloud backup service.
These types of incidents can cause numerous problems for a business, from loss of revenue to legal repercussions and a diminished brand reputation.
Implementing robust DLP software is how you mitigate these risks and protect your organization from data loss incidents.
What Are the Three Types of DLP?
The three types of DLP (Data Loss Prevention) software are network, endpoint, and cloud:
- Network DLP monitors and protects data while it’s in transit over the network.
- Endpoint DLP secures data on individual devices.
- Cloud DLP protects stored data in cloud-based applications and services.
What Are the Common DLP Use Cases?
Some common DLP use cases include protecting intellectual property, securing customer data, and preventing insider threats.
What Should You Look for in a DLP Tool?
When you’re choosing a DLP solution, you need to find a system that aligns with how your organization manages and protects data.
Typically, you’d want a platform that provides a mix of context-aware visibility, policy flexibility, and intelligent automation that scales with your security posture.
Some other core capabilities include:
Data Discovery and Classification
This is mainly about knowing where your sensitive data resides. A strong DLP platform automatically identifies and classifies data across file shares, email systems, cloud applications, endpoints, and on-premises repositories.
This visibility helps organizations understand their data footprint and enforce the right policies before a breach ever occurs.
Some more advanced tools (like Teramind) use machine learning and content inspection to identify sensitive data, even when it’s hidden in unstructured formats such as PDFs, images, or chat logs.
Policy Creation and Enforcement
This allows you to build customizable policies that fit your business model, whether that’s protecting financial records, customer PII (Personally Identifiable Information), healthcare data, or intellectual property.
What you’re looking for are context-aware policies that adapt dynamically based on user role, data type, location, and risk level.
Real-Time Monitoring and Protection
A good DLP tool should provide real-time monitoring for both data in motion (as it travels across the network) and data at rest (stored on devices or servers).
This helps security teams stop unauthorized data movements or downloads before they become incidents.
In addition, look for tools that can apply automated controls, such as blocking or encrypting data based on predefined rules.
Remediation Workflows and Incident Response
Opt for solutions that include automated remediation workflows and incident response playbooks that trigger alerts, assign cases, and guide analysts through resolution steps.
Some tools integrate directly with SOAR (Security Orchestration, Automation, and Response) platforms to accelerate response time, close feedback loops, and learn from recurring incidents.
Behavior Analytics and User Insights
False positives can harm productivity. That’s why your preferred DLP platform should integrate User and Entity Behavior Analytics (UEBA) to understand how employees normally interact with data.
For example, when activity deviates from the norm, such as a user downloading an unusually large volume of files, the system should flag it for review or automatically restrict access.
Integration and Ecosystem Compatibility
Finally, a solid DLP solution should connect seamlessly with your broader security ecosystem, including SIEM, CASB, EDR, IAM, and threat intelligence platforms.
This is a good capability for large enterprises managing hybrid environments, as it offers centralized alerting and coordinated response across tools.
How Do You Select the Best DLP Tool for Your Organization?
When selecting the best DLP tool for your organization, you must make sure it aligns with your security needs and business objectives.
Here’s a detailed breakdown of the steps and considerations involved:
Understand Your Data
Before choosing a DLP tool, it’s crucial to clearly understand the types of data your organization handles.
Identify where your data resides, how it moves within and outside your organization, and its sensitivity level. This will help you determine the scope and scale of the DLP solution needed.
Define Your Data Protection Goals
Outline what you want to achieve with a DLP tool.
Goals may include protecting intellectual property, complying with regulations (like the GDPR and HIPAA), or preventing data breaches.
Clearly defined goals will guide your choice of features and capabilities in a DLP tool.
Evaluate Key Features
Different DLP tools offer different features; selecting the right tool depends on the features that best meet your needs.
Essential features to consider are:
- Content Discovery: The ability to scan and identify sensitive data across various locations.
- Data Monitoring: Real-time monitoring of data usage and movement.
- Incident Response and Alerts: Automated responses and alerts for policy violations.
- Integration Capabilities: Compatibility with your existing security tools and IT infrastructure.
- Ease of Policy Enforcement: The best DLP tools facilitate straightforward policy creation and enforcement.
Consider Deployment Options
DLP solutions can be deployed on-premises, in the cloud, or as a hybrid model. Each option has its pros and cons:
- On-Premises: Offers control over physical infrastructure but requires significant maintenance and upfront costs.
- Cloud-Based: Provides scalability and lowers initial costs but may raise concerns about data sovereignty and security.
- Hybrid: Combines the benefits of both on-premises and cloud, making it suitable for organizations transitioning to the cloud.
Assess Compliance Requirements
Ensure that your chosen DLP tool helps you meet the regulatory requirements relevant to your industry.
The tool should facilitate compliance with all applicable data protection and privacy laws and standards.
Vendor Reputation and Support
Research potential vendors’ reputations, focusing on their stability, customer support, and the robustness of their security measures.
Vendor support is crucial, as it affects the implementation phase and ongoing maintenance of your DLP tool.
Test and Evaluate
Before making a final decision, it’s advisable to test the shortlisted DLP tools in your environment.
Pilot testing will help you see how well each tool integrates with your systems and meets your expectations.
Cost Consideration
Analyze the total ownership cost, including licensing, implementation, training, and maintenance costs.
Opt for a tool that offers the best value for money within your budget.
User Reviews and Feedback
Look at feedback from other users, especially those in similar industries.
User reviews can provide insights into a DLP tool’s real-world effectiveness. They can also highlight issues and advantages you might not have considered.
What is the Future of DLP?
The future of DLP is being shaped by how and where organizations handle data.
Information is no longer confined to on-premises servers. Now, it’s flowing freely between cloud apps, hybrid workspaces, and remote devices.
And here’s how it’s all going to unfold in 2026:
Growing Role of AI and Machine Learning
Traditional DLP relied heavily on keyword matches and rigid policy rules, which limited scalability and accuracy for large enterprises.
Meanwhile, with AI and machine learning, DLP is becoming more adaptive and predictive. Modern systems can now learn from user behavior, detect intent, and identify risks before data leaves the environment.
They correlate unusual actions with risk signals and automatically trigger real-time responses. This level of automation reduces false positives and lightens the workload for already stretched security teams.
Shift Toward Cloud-Native and SaaS-First DLP Solutions
According to Gartner, by 2026, over 70% of enterprise data will reside in cloud platforms and SaaS applications. This trend is pushing more organizations to embrace multi-cloud infrastructures and remote collaboration.
Modern DLP tools are being designed to accommodate this reality. The goal is to provide unified visibility across endpoints, cloud apps, email, and web gateways without heavy on-premises infrastructure.
Behavior Analytics and Insider Risk Management
Human behavior remains the most unpredictable variable in cybersecurity, and also the biggest source of data breaches. Studies show that roughly 95% of successful cyber-attacks are a result of human error.
The new generation of DLP tools puts user intent and behavior analytics at the core of their design. By understanding normal activity patterns, they can identify when something changes. This way, organizations can catch risks early, coach employees in real time, and build a security-aware culture.
The Impact of Zero Trust, Encryption, and Real-Time Monitoring
Zero trust replaces the assumption of trust with continuous verification. This is to ensure that every user, device, and data movement is validated.
Encryption is the final safeguard. Regardless of the stage (in transit, in use, or at rest), it ensures that even if an attacker or insider gains access, the data remains unreadable and unusable.
When you combine all of this with real-time visibility into how data flows across an enterprise, it creates a security posture where prevention and detection are seamless.
Which is the Best Data Loss Prevention Tool?
When it comes to protecting your organization’s most sensitive assets, Teramind consistently ranks as the best DLP software on the market. While traditional tools rely on static, easily bypassed rules, Teramind uses advanced behavioral analytics to understand the human element of security.
By establishing baseline user behavior patterns, Teramind identifies and blocks sophisticated data exfiltration attempts that other systems miss — all while reducing false positives that often overwhelm security teams.
Try Teramind’s DLP tool for yourself → Interact with a live deployment

