With employees using so many different devices and applications at work, it’s getting harder for companies to maintain visibility and control. User activity monitoring (UAM) software has emerged as a critical tool, empowering businesses to safeguard against data breaches, insider threats, and low productivity.
This guide compares the top user activity and employee monitoring software solutions available today. We’ll look at key features, use cases, customer reviews, and pricing to help you make an informed decision.
What Are User Activity Monitoring Tools?
User activity monitoring (UAM) tools are software solutions that allow organizations to track and analyze how employees interact with company systems, applications, and data.
These platforms capture behavioral data — such as website usage, application tracking, and file transfers — to help businesses improve productivity, ensure regulatory compliance, and protect against insider threats.
How Did We Select the Best User Activity Monitoring Solutions?
To curate this list of the best tools for monitoring employee activity, we didn’t just look at the most popular names. Our selection process involved a rigorous, data-driven methodology to ensure that every recommendation delivers genuine value, security, and insight.
We evaluated dozens of solutions against the following key criteria to find the perfect balance between performance management and employee trust:
- Core Feature Robustness: We prioritized tools that offer more than just simple time tracking. Our top picks include advanced capabilities like AI-powered behavioral analytics, real-time screen recording, Optical Character Recognition (OCR), and comprehensive Data Loss Prevention (DLP) modules.
- Industry-Specific Fit: Different sectors have different needs. We selected tools that cater to diverse environments — from high-security financial institutions requiring deep forensic logs to creative agencies seeking non-invasive productivity metrics.
- Privacy and Compliance Standards: Every tool on this list was vetted for its ability to help organizations meet global regulations like the GDPR, HIPAA, and SOC 2, including privacy-first controls like screenshot blurring and selective monitoring.
- User Reviews and Market Reputation: We analyzed verified user experiences from platforms like Capterra and G2. We looked for consistent praise regarding reliability, ease of setup, and responsive customer support.
- Usability and Integration: We focused on platforms with intuitive dashboards, minimal system resource impact, and seamless “plug-and-play” integrations with existing tech stacks like Jira, Slack, and various HRIS systems.
- Scalability and Value: We evaluated pricing models to ensure they offer a strong Return on Investment (ROI), with flexible tiers that don’t lock essential features behind paywalls.
What Are the Best User Activity Monitoring Tools?
1. Teramind
Teramind is a leading workforce analytics and insider risk management platform that helps organizations streamline operations while securing sensitive data.
It provides a unified approach to user activity monitoring by transforming behavioral data into actionable business intelligence. Whether you’re a small business or an enterprise, Teramind offers high-performance tools to optimize your workforce, improve business processes, and identify productivity trends in real-time.
As a comprehensive cybersecurity solution, Teramind excels at mitigating insider threats and preventing data breaches through sophisticated behavioral telemetry and predictive analytics. With granular configurability and privacy-friendly deployment models, Teramind allows administrators to monitor file sharing, track application usage, and receive instant alerts on risky user behavior.
Key Features
See Teramind’s capabilities all in one place → Take an interactive product tour
- Real-Time Live View and Historical Playback: Monitor live work screens or review past activities via historical recordings to gain a complete understanding of employee activity.
- AI Agent Governance: Gain full visibility into how your workforce uses generative AI tools like ChatGPT, Microsoft Copilot, and Google Gemini. Teramind tracks prompts and responses and can detect unauthorized Shadow AI applications.
- Smart Rules and Automated Alerts: Implement automated compliance rules that flag or block risky behavior in real-time, such as sharing sensitive data like SSNs or violating HIPAA and GDPR policies.
- Optical Character Recognition (OCR): Search for and extract text from images and video screenshots, significantly enhancing your data discovery and audit capabilities.
- Employee Productivity Tracking: Log active versus idle time and perform deep-dive analyses into unproductive work hours, helping you to refine workflows and identify skill development opportunities.
- Comprehensive Activity Monitoring: Track a wide range of user actions across email, instant messaging, social media, and file transfers to prevent data leaks and ensure policy adherence.
- Remote Desktop Control (RDP): Securely take control of remote endpoints to provide instant technical support or intervene during a live security incident.
- Enterprise Integrations: Seamlessly connect Teramind with your existing tech stack, including ServiceNow, Splunk, Jira, and Tableau, for centralized productivity analysis.
Best For
Organizations of any size that require a total, high-performance solution for security, productivity, and compliance.
Teramind is especially valuable for those needing to mitigate insider threats and prevent data breaches.
What Teramind Users Say
“Its intuitive interface and comprehensive monitoring capabilities make it easy to track and analyze user activity effectively. The real-time alerts and detailed reports help quickly identify risks and ensure compliance, enhancing overall security.” See Full Review →
Pricing
Test Teramind before committing → Explore a live online demo
Teramind offers several pricing tiers to accommodate businesses of different sizes and feature requirements:
- Starter ($14/seat/month): Best for basic productivity use cases and identifying risky users. Includes quick visual evidence capture, live playback, and website/app tracking.
- UAM ($28/seat/month): Designed for comprehensive productivity optimization and security detection. This tier includes everything in Starter plus full digital activity telemetry, UEBA (User and Entity Behavior Analytics), forensics, and unlimited behavior rules.
- DLP ($32/seat/month): Best for comprehensive intent-based security detection and response. It includes everything in UAM plus content-based data exfiltration prevention and automated actions to block data leaks in real-time.
- Enterprise (Custom pricing): Tailored professional services for the most demanding large-scale enterprises and government organizations. Includes everything in DLP plus in-app parsing for fraud detection, an OCR engine, and unlimited activity-based behavior rules.
All paid plans shown above reflect an 8% discount for annual billing compared to the monthly rates.
2. ActivTrak
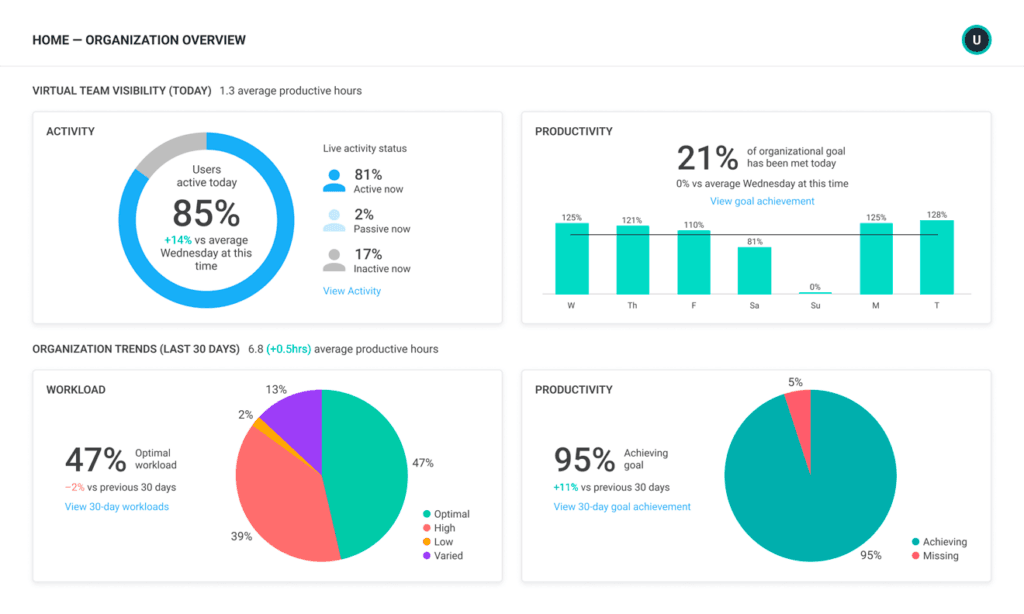
ActivTrak is a cloud-based workforce analytics platform that gives businesses visibility into employee activity and work habits.
The software tracks employees’ computer usage, including the applications and websites they access and the time spent on various tasks. This workforce data can be used to identify areas for improvement, optimize productivity levels, and ensure compliance with company policies.
Key Features
See how Teramind compares to ActivTrak →
- Real-Time Productivity Monitoring: Gain an immediate view of employee activity, including which apps they’re using and how productive they are at any given moment.
- AI Usage and Governance: Track how your workforce adopts AI tools like ChatGPT, Claude, and Gemini. Measure the impact of AI on capacity and ensure compliance across all LLM interactions.
- Schedule and Location Adherence: Monitor work trends across hybrid and remote work environments, including productivity by location and adherence to established schedules.
- Privacy-First Monitoring: ActivTrak is built for transparency, intentionally excluding features like keystroke logging, email monitoring, video recording, or camera access.
Best For
Companies focused on optimizing productivity levels and ensuring employees adhere to policies.
ActivTrak is well-suited for leaders who want visibility into work patterns across hybrid and remote environments without using invasive features like keystroke logging.
What ActivTrak Users Say
“It helps us understand what websites our team uses often and also tells us how much time our associates spend on each site. Tracking of productivity works well, allowing us to identify areas needing improvement and understand our technology use.” See Full Review →
Pricing
ActivTrak offers a variety of pricing plans to suit different needs, from a Free version with basic time tracking to a Professional plan for enterprise users. Costs start at $10 per user per month when billed annually.
3. Hubstaff
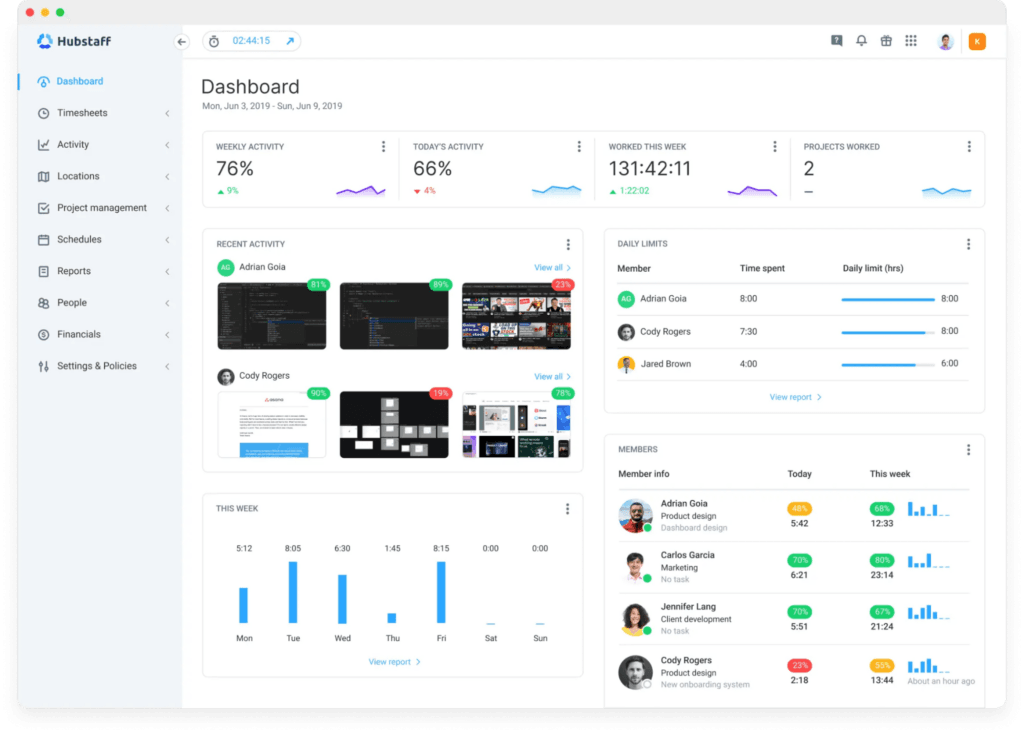
Hubstaff is a time tracking and productivity monitoring tool designed to optimize the efficiency of remote and hybrid workers. It offers automated time tracking processes, workforce analytics, flexible payroll, project cost management, and actionable employee productivity data.
The software is particularly suited for remote workforce management, including payroll, attendance tracking, and invoicing processes.
Key Features
See how Teramind compares to Hubstaff →
- Smart Time Tracking: Streamline how your employees log work hours across every project and task using web browsers or dedicated apps for desktop, Android, and iOS.
- Online Timesheets and Approvals: Automatically generate detailed timesheets that managers can review, approve, or reject with a single click.
- Customizable Screenshots: Gain visibility into work as it happens with screenshot capturing, which includes a “blur” option to safeguard sensitive personal data.
- App and URL Monitoring: See exactly which applications your team uses and which URLs they visit while the Hubstaff timer is active.
Best For
Businesses managing remote or mobile teams.
Hubstaff is a great fit for organizations that need automated payroll, invoicing, and attendance tracking integrated with their productivity data.
What Hubstaff Users Say
“The monitoring features and analytics are really helpful for us since our company is made up entirely of remote workers. I also really like the smart notifications, along with the real-time shift and schedule tracking.” See Full Review →
Pricing
Hubstaff offers four paid pricing plans: Starter ($4.99 per user per month), Grow ($7.50 per user per month), Team ($10 per user per month), and Enterprise ($25 per user per month). You can pay extra for add-ons or select a 14-day free trial.
4. SoftActivity
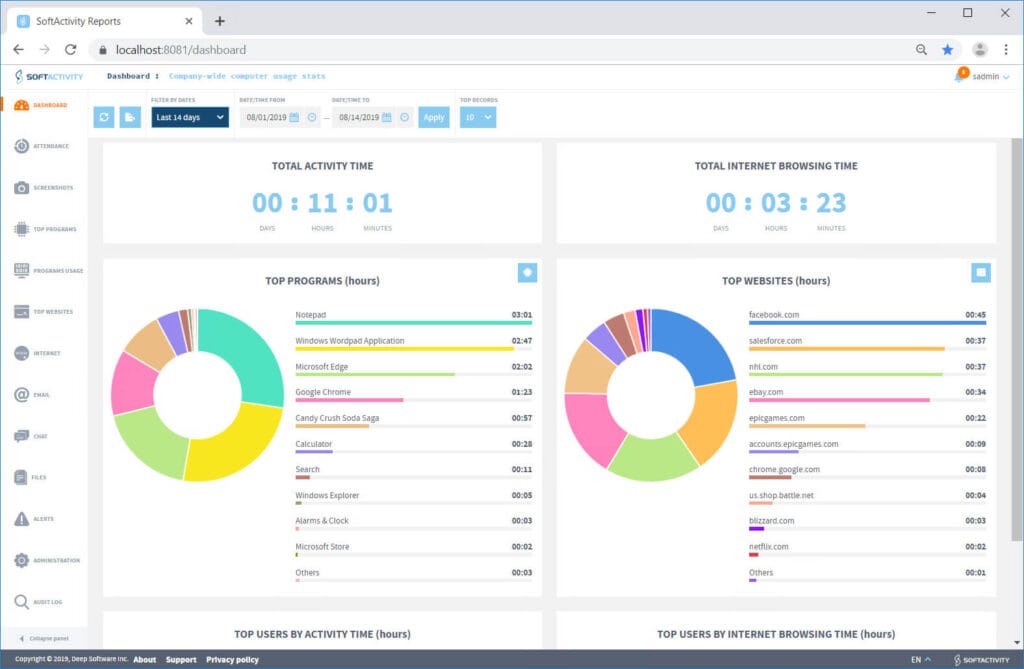
SoftActivity is a user activity monitoring solution that offers visible and stealth mode options. Unlike some workforce analytics tools that focus purely on productivity charts, SoftActivity digs into forensic details, offering features like screen recording, keystroke logging, and website history tracking — even if the user deletes their browser history.
It’s available as both a cloud-based SaaS (SoftActivity Work) and an on-premise solution (SoftActivity Monitor), making it a versatile choice for companies that prefer to keep their data within their own local network.
Key Features
- Real-Time Remote Desktop View: Managers can view the live desktops of multiple users on a single screen, similar to a security camera feed.
- Internet and App Tracking: The software records all visited URLs — including those in Incognito/InPrivate mode — and generates “Top Websites” and “Top Programs” reports based on total time spent.
- Keystroke Logging and Communication Recording: Capture real-time keystrokes across all applications and websites, while also recording emails and other digital communications to protect against IP theft.
- Screenshot Capture and Playback: Get a complete timeline of screenshots for every user action, providing definitive evidence for incident responses.
Best For
Organizations that require stealth monitoring and highly detailed forensic logs to investigate potential insider threats.
Because it offers an on-premise deployment option, SoftActivity is a versatile choice for companies that prefer to keep their sensitive monitoring data within their local network.
What SoftActivity Users Say
“A great product that makes monitoring staff activity easy. Staff are aware that they are being monitored and this quickly improves their focus to work smarter.” See Full Review →
Pricing
SoftActivity’s pricing is based on its deployment options. Its on-premise solution, SoftActivity Monitor, is available as a perpetual license in either standard or enterprise editions, and with different terms of update and support. Its SaaS solution, SoftActivity Work, is available as a monthly or annual subscription; costs vary depending on the number of monitored users.
5. EmpMonitor
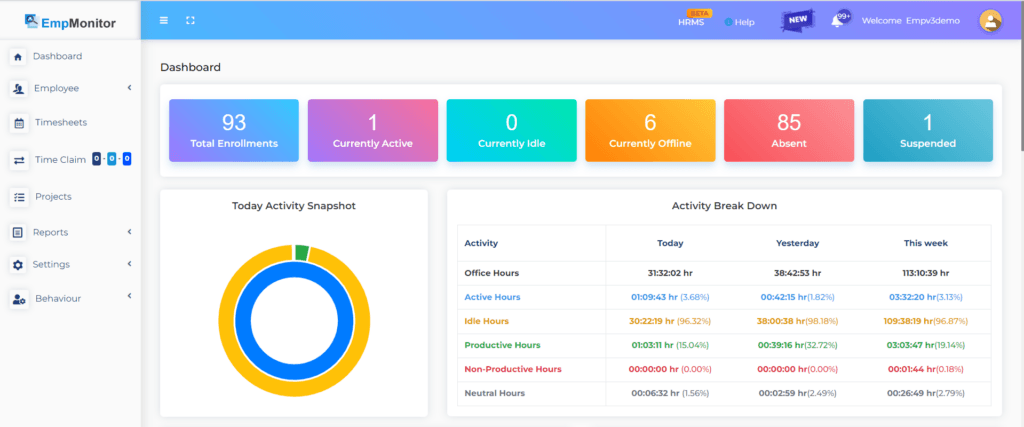
EmpMonitor is an open-source user activity monitoring and productivity platform designed to help modern, distributed teams gain full visibility into their operations.
This “all-in-one” solution transforms behavioral data into actionable insights, allowing businesses to maximize workforce efficiency while maintaining high standards of data security. With a focus on simplicity and transparency, it offers real-time tracking across major operating systems, including Windows, Mac, and Linux/Ubuntu.
Key Features
- Real-Time User Activity Monitoring: Gain instant visibility into your team’s workflow with a unified dashboard that tracks live application usage, website visits, and active or idle statuses.
- Stealth Mode Operations: Monitor with minimum software exposure; with this setting, the app doesn’t appear in program lists or web histories, ensuring unbiased activity data.
- Insider Threat Prevention and DLP: Protect sensitive data by blocking unauthorized USB devices and restricting access to compromised or restricted platforms.
- Project and Task Management: Streamline project planning by assigning tasks and tracking milestones through detailed progress reports and precise resource allocation.
Best For
Distributed teams looking for an all-in-one guardian for productivity and workforce management.
EmpMonitor’s support for Windows, Mac, and Linux/Ubuntu makes it a flexible option for diverse technical environments.
What EmpMonitor Users Say
“HR can more easily track productivity without doing any manual work thanks to EmpMonitor’s automated attendance and keystroke logging features.” See Full Review →
Pricing
EmpMonitor offers plans for teams of all sizes, with costs starting at $11 per user per month for teams of 1 to 10 users. A 15-day free trial is included with all packages.
6. Controlio
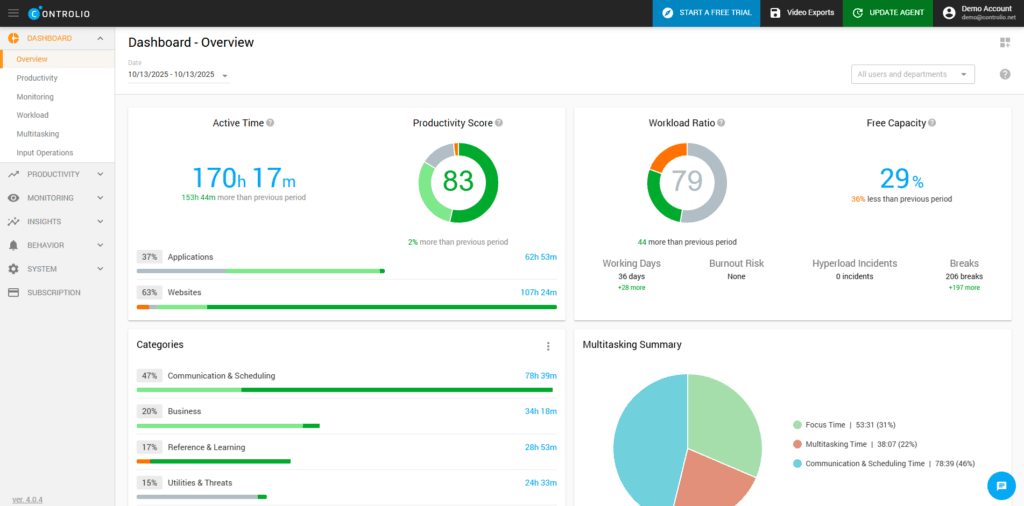
Controlio is a cloud-based computer monitoring software designed to track employee productivity and behavior in real-time.
It offers a range of features, including live view screen monitoring, screen recording, app and web usage tracking, compliance with global data protection regulations, and an optional stealth mode.
Key Features
- AI-Powered Productivity Scoring: Automatically track productive versus distractive activities and calculate productivity scores for individual users and entire departments.
- User Behavior Analytics: Dig into automated logs and clear-cut visualizations to learn how productive your staff is at micro and macro levels.
- Real-Time Live View: Gain immediate oversight by viewing users’ screens via Controlio’s web-based dashboard.
- Application and Website Tracking: Monitor exactly which tools and sites your staff is using.
Best For
Businesses seeking flexible, real-time monitoring options that ensure compliance with strict global regulations like HIPAA and GDPR.
Controlio is particularly effective for leadership teams that want to use AI-powered scoring to pinpoint time-intensive tasks and rebalance workloads across departments.
What Controlio Users Say
“The useful feature of Controlio is the ability to see how time is distributed across tasks and tools. This makes it easy to identify bottlenecks and inefficiencies in our workflows. The reports are detailed enough to provide insights without being too complicated.” See Full Review →
Pricing
Controlio offers two main pricing packages: Basic ($6.67 per user per month) and Advanced ($9.99 per user per month). Enterprise customers must request bespoke pricing. You can also take advantage of a 14-day free trial.
7. InterGuard
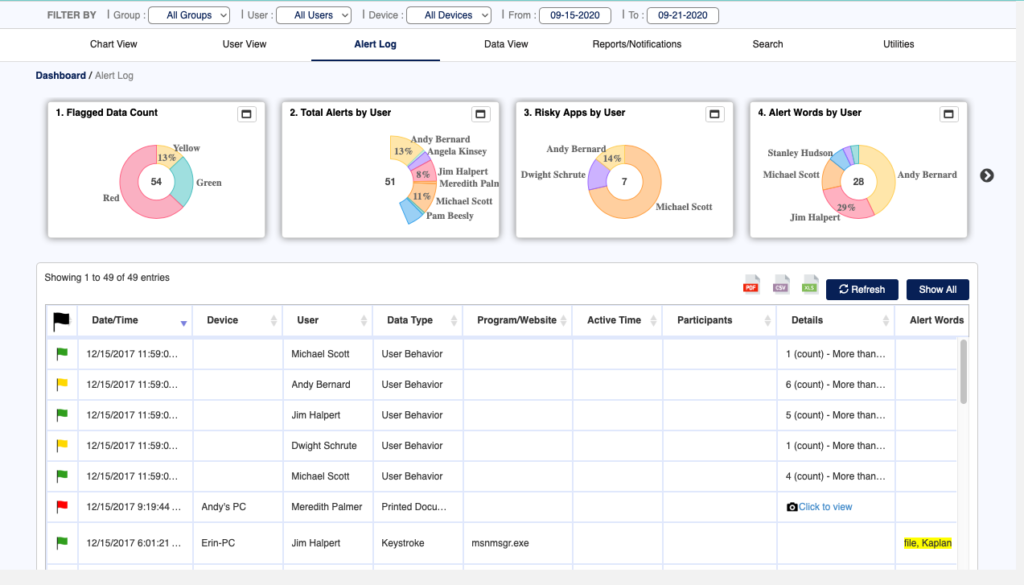
InterGuard is an employee monitoring software that offers tools for time tracking, insider threat detection, and data loss prevention.
The software records user actions, including web browsing, application usage, email communications, and file transfers, providing employers with real-time insights into their workforce’s productivity and behavior.
Key Features
- Employee Time and Attendance Tracking: Simplify your workforce management with automated tracking that starts the moment the InterGuard app is installed, providing robust reports on daily activity.
- Comprehensive Email Monitoring: Monitor employee communications across a wide range of platforms, including Outlook, Gmail, Office 365, and even LinkedIn InMail.
- Smart Alert System: Receive instant, automatic email notifications when pre-defined risky activities occur.
- Social Media Accountability: Keep distractions to a minimum by monitoring social media usage during work hours, ensuring a fair and productive environment for all employees.
Best For
Organizations needing deep, high-context insights into workforce behavior, such as email communications and file transfers.
InterGuard is a strong choice for security-conscious firms that require endpoint lockdown and remote data retrieval.
What InterGuard Users Say
“The support provided by InterGuard is one of the best – from sales to support. The fact that it also has both DLP and endpoint lockdown features is a major bonus.” See Full Review →
Pricing
InterGuard doesn’t disclose its pricing online. You must complete a form on its website to receive a quote.
8. Time Doctor
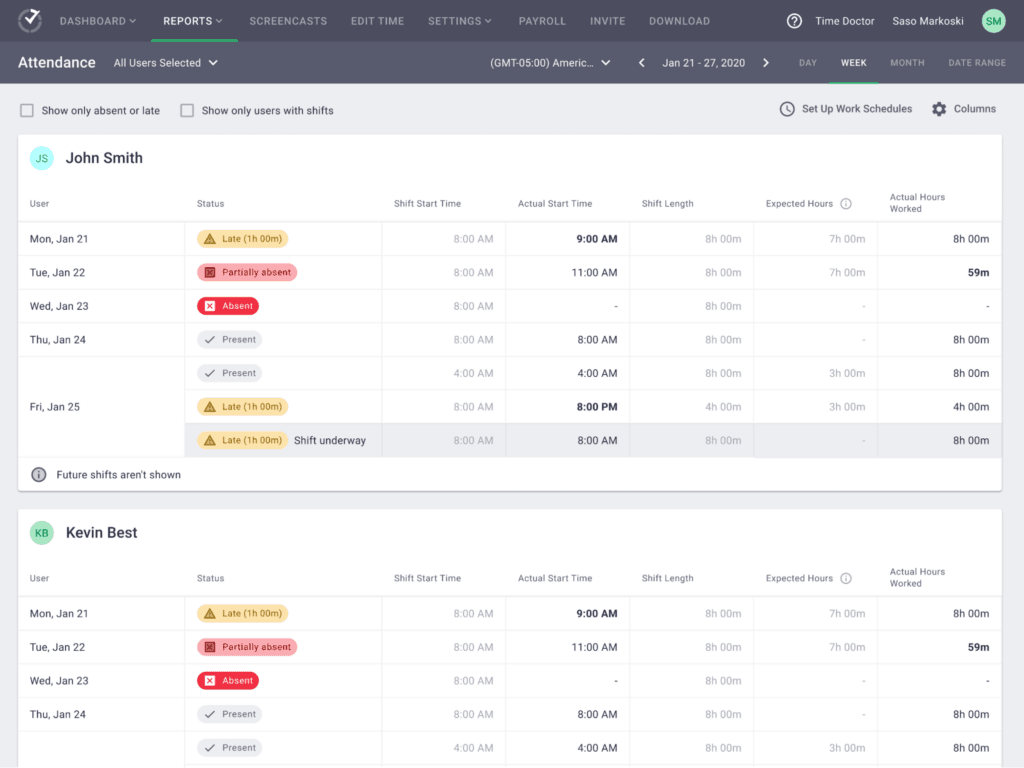
Time Doctor is a SaaS workforce analytics platform that provides insights into employee time management and work patterns.
It offers real-time tracking and user behavior analytics, helping businesses to improve performance and well-being for in-office, hybrid, or remote workers.
Key Features
See how Teramind compares to Time Doctor →
- Automatic and Manual Time Tracking: Capture work hours accurately across various locations and schedules, with the flexibility to choose between automated logging or manual control.
- Benchmarks AI: Compare your team’s work patterns against AI-matched peer groups to understand where your organization stands relative to industry averages.
- Work-Life Balance and Wellness: Identify early signs of employee burnout or overload by monitoring workload patterns, long hours, and after-hours activity.
- Real-Time Dashboards: Access role-based dashboards that provide live visibility into tasks, shifts, and productivity metrics for both managers and employees.
Best For
Companies looking to optimize performance and well-being across remote, in-office, or hybrid teams.
Its unique monitoring features, such as Benchmarks AI and work-life balance measurement, help managers identify employee burnout while comparing team patterns against industry averages.
What Time Doctor Users Say
“The tracking and reporting features give me a clear breakdown of how time is spent on different tasks and projects. Additionally, the initial setup is very straightforward and easy.” See Full Review →
Pricing
Time Doctor offers several pricing tiers with either limited or advanced features. Costs start at $6.67 per user per month for the Basic package. Enterprise customers can request bespoke pricing. All plans include a 14-day free trial with no credit card required.
9. Insightful
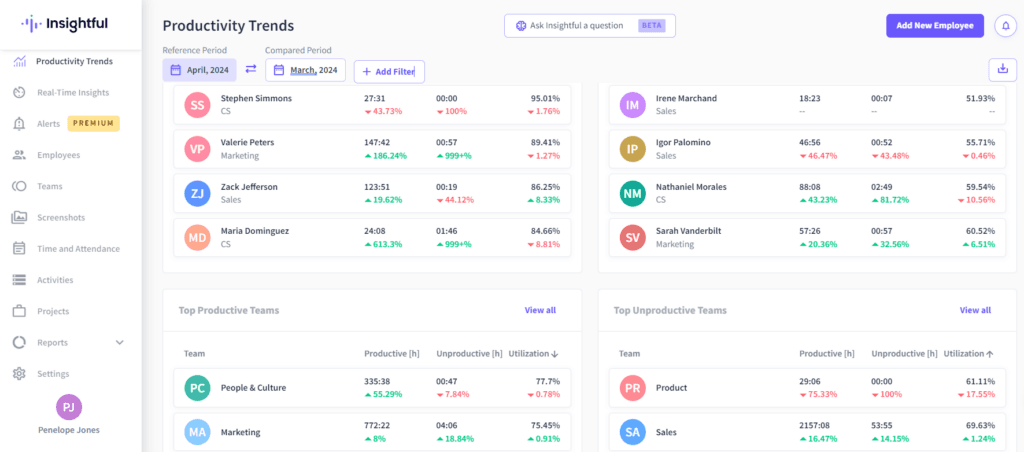
Insightful is a workforce analytics and productivity platform that provides actionable data insights, enabling teams to work more efficiently.
It offers features like employee productivity monitoring, automatic time tracking, and remote team management, all within a secure, easy-to-use interface.
Key Features
- Smart Workload Management: Rebalance tasks in real-time by spotting uneven workloads and bottlenecks, helping to prevent employee burnout before it starts.
- Software and Tool Utilization: Cut software costs by identifying unused licenses and shrinking your technology stack based on real usage data.
- Automatic Time and Attendance: Capture precise work hours, including active, idle, and break time, to ensure clean audits and more effective people management.
- Project and Task Tracking: Understand exactly where time goes on specific projects to improve operational efficiency and slash project timelines.
Best For
Teams seeking to improve operational efficiency through automated time tracking and actionable, data-driven insights.
Insightful is well-suited for organizations that need to manage work-from-home schedules automatically.
What Insightful Users Say
“What I like most about Insightful is the automatic time tracking without manual input, which ensures accurate reporting for my employer. The automatic identification of inactivity is also beneficial for accurate time reporting.” See Full Review →
Pricing
Insightful offers plans based on its main use cases, including Workforce Analytics, Workflow Optimization, or a combination of the two. Custom pricing for enterprises is available. Costs start at $10 per user per month. You can also sign up for a 7-day free trial.
10. CurrentWare
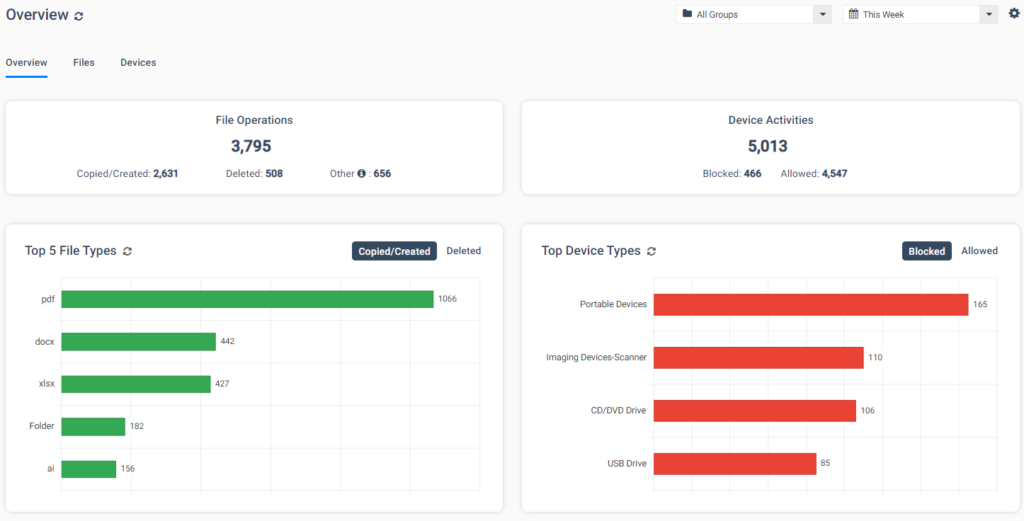
CurrentWare is a modular endpoint security suite designed to give organizations flexibility in how they monitor and control user activity. Rather than buying a massive “all-in-one” platform, CurrentWare allows you to purchase specific modules — such as BrowseReporter for activity monitoring or AccessPatrol for USB data control.
This approach makes it an excellent choice for small to medium-sized businesses (SMBs) and educational institutions that need specific controls (like web filtering or bandwidth monitoring) without paying for features they won’t use. CurrentWare tracks web browsing, application usage, and bandwidth consumption to identify productivity bottlenecks.
Key Features
- Web Filtering and Management: Block websites based on specific URLs or content categories and utilize allow/block lists to strictly control internet access.
- Data Theft Prevention and Device Control: Prevent data leaks by blocking unauthorized USB devices, network storage, and other peripherals while receiving alerts for unknown device connections.
- Screenshot Monitoring: Automatically capture desktop screenshots or utilize remote desktop viewing to obtain detailed evidence of employee activity.
- File Transfer Security: Block file transfers based on specific file names or types and generate DLP activity reports to track file operations and storage device use.
Best For
Small-to-medium businesses (SMBs) and educational institutions requiring a flexible, budget-friendly solution.
CurrentWare’s pick-and-choose module approach allows these organizations to implement controls like web filtering or USB data protection without paying for an entire platform.
What CurrentWare Users Say
“It’s easy to deploy and control USB access on all of our PCs on-site. I don’t have to worry about foreign devices from being plugged in. I can also restrict devices such as printers where they are not needed.” See Full Review →
Pricing
You can purchase CurrentWare’s modules separately or as a complete package. Each module is priced at $6 per user per month. The total suite is currently on offer at $14 per user per month. You can test CurrentWare’s products with a 14-day free trial.
11. DeskTime
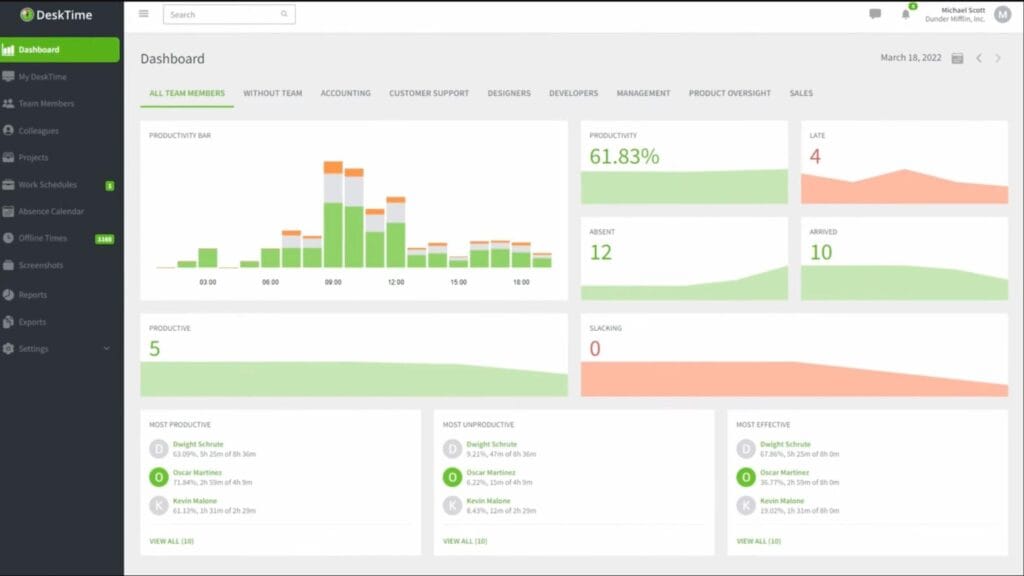
DeskTime is an all-in-one time tracking platform designed to support remote, hybrid, and distributed teams.
The platform’s core philosophy centers on a “set it and forget it” approach, utilizing fully automatic tracking that runs quietly in the background without interrupting a team’s natural workflow. By capturing real work patterns, DeskTime helps organizations eliminate time waste and reach their goals faster.
Key Features
See this list of DeskTime alternatives and competitors →
- Automatic Time Tracking: The desktop application tracks all computer activities automatically, eliminating the need for manual start and stop buttons.
- URL and App Tracking: Gain visibility into exactly which websites and applications your team uses throughout the workday.
- Productivity Calculation: Automatically categorize activities as productive, neutral, or unproductive to spot your top performers and identify areas for improvement.
- User Dashboards: Empower team members with in-depth information about their own performance, helping them set personal productivity goals.
Best For
Teams looking for a non-intrusive, “set it and forget it” time tracker that focuses on productivity and project costs.
DeskTime is best for managers who want a fully automated way to categorize activities and empower employees to track their own performance goals.
What DeskTime Users Say
“I like the ease of use and that you can add integrations, such as Google Calendar, to synchronize your meetings with the time tracker at work. It also has online support to solve any kind of problem.” See Full Review →
Pricing
DeskTime offers three pricing tiers: Pro (for small teams and startups), Premium (for hybrid and growing teams), and Enterprise (for large organizations). Your first month is free if you select annual billing. You can also sign up for a 14-day free trial.
12. KeepActive (formerly Kickidler)
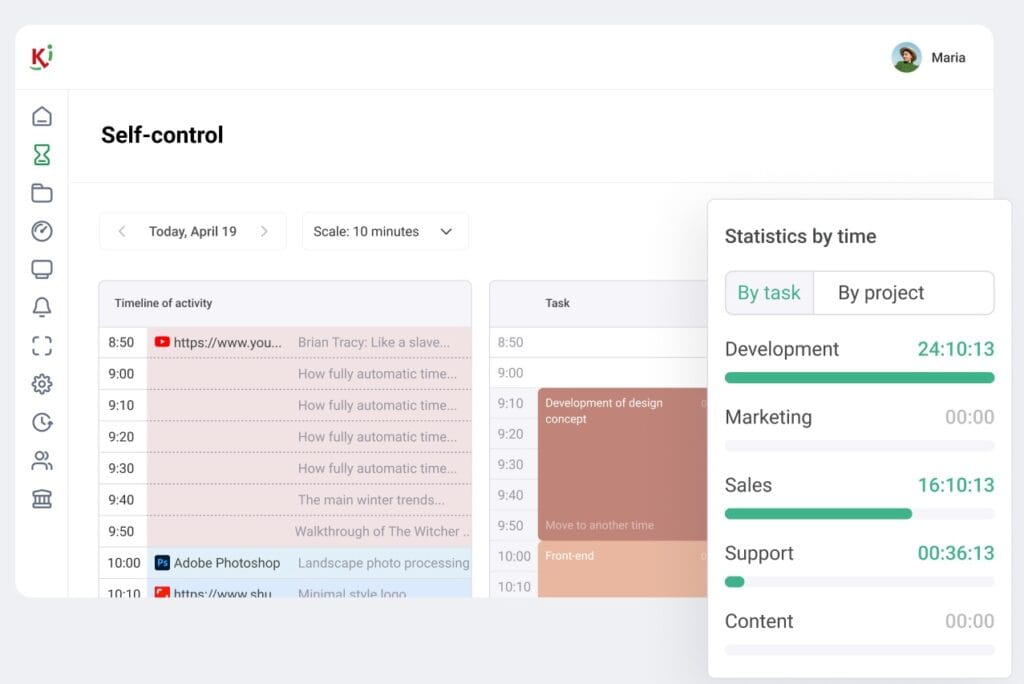
KeepActive (formerly known as Kickidler) is a leading employee monitoring and workforce analytics platform.
Designed as a cross-platform solution for Windows, Mac, and Linux, it provides businesses with visibility into team activities through automated data collection and visual monitoring. By combining real-time screen tracking with powerful reporting, KeepActive helps managers optimize business processes, protect sensitive data from malicious intent, and boost team productivity.
Key Features
See this list of KeepActive alternatives and competitors →
- Real-Time Visual Monitoring: Managers can view an unlimited number of employee screens online simultaneously to identify who is active, absent, or committing a violation.
- Productivity and Efficiency Analysis: Classifies activities as productive, neutral, or unproductive, providing specific reports on work dynamics and overall employee performance ratings.
- AI-Powered Protection: Utilizes artificial intelligence to detect and block unauthorized photographing of computer screens.
- Geofencing and Geolocation: Tracks the physical location of devices via IP addresses and geolocation technology to prevent data access from unauthorized areas.
Best For
Organizations aiming to boost productivity while protecting data via behavioral analytics.
KeepActive is particularly suited for high-security environments that require cutting-edge Al protection, such as detecting if someone is attempting to take a photo of a computer screen.
What KeepActive Users Say
“It is a very practical system to use and easy to control. With it, I can manage users and monitor performance reports throughout the week, which helps me understand each one’s productivity.” See Full Review →
Pricing
KeepActive offers pricing plans with different levels of features, including Time Tracking ($2.75 per user per month), Employee Monitoring ($5.50 per user per month), and Data Loss Protection ($11 per user per month).
How Do the Best Enterprise Data Security Tools Compare?
| Tool Name | Description | Best For |
|---|---|---|
| Teramind | Comprehensive UAM solution offering robust monitoring for insider threat detection, productivity optimization, and data loss prevention. | Best overall tool for organizations seeking a complete solution for security, productivity, and compliance needs. |
| ActivTrak | Cloud-based workforce analytics platform that provides visibility into employee productivity, activity, and work patterns. | Companies looking to optimize productivity levels and ensure compliance with company policies. |
| Hubstaff | Time and productivity tracking tool designed for remote, mobile, and growing workforces. | Businesses managing remote teams and seeking to streamline workforce management processes. |
| SoftActivity | On-premise and cloud-based monitoring solution focused on activity tracking, including key logging and stealth mode operations. | Organizations requiring stealth monitoring and detailed forensic logs for insider threat investigations. |
| EmpMonitor | An open-source, SOC 2 Type 2 certified platform providing 360-degree visibility through live screencasting, automated screenshots, and time tracking across Windows, Mac, and Linux. | Distributed teams seeking an all-in-one productivity guardian and secure workforce management solution. |
| Controlio | Cloud-based computer monitoring software for real-time employee productivity tracking. | Businesses seeking flexible monitoring options and compliance with regulations like HIPAA and GDPR. |
| Interguard | Employee monitoring software designed to track and record employee productivity with insider threat detection. | Organizations needing detailed insights into workforce productivity and behavior. |
| Time Doctor | SaaS workforce analytics platform designed to enhance productivity by providing insights into employee time management. | Companies looking to optimize performance across remote, in-office, or hybrid teams. |
| Insightful | Workforce analytics and productivity platform providing actionable data insights and automatic time tracking. | Teams seeking to improve efficiency through data-driven insights and automated time tracking. |
| CurrentWare | Modular UAM suite that offers granular internet usage tracking, bandwidth monitoring, and power management. | SMBs and educational institutions looking for a modular, budget-friendly monitoring solution. |
| DeskTime | Fully automated time tracker focusing on productivity and project costs. | Teams seeking simple, non-intrusive productivity analytics and efficient resource allocation. |
| KeepActive | A workforce analytics and DLP suite featuring real-time visual monitoring, AI-powered screen photo protection, and specialized self-monitoring tools. | Organizations looking to boost productivity and protect data through advanced behavioral analytics and automated monitoring. |
What Features Should You Look for in User Activity Monitoring Software?
At a minimum, the user activity monitoring solution you choose should feature the following capabilities:
- Features for maintaining productivity, enhancing security, ensuring compliance, or (ideally) all three.
- Advanced analytics that monitor activity on an ongoing basis according to organizational parameters.
- Extensive customizability that enables managers to tailor the solution to their needs.
- Trend and pattern analysis that places employee productivity and data security within a wider context.
Features for Increasing Employee Productivity
When boosting productivity is the highest organizational need, look for tools that include these features:
- Personalized dashboards to track and measure the user activity that matters most.
- The ability to monitor all users from anywhere in the world, including remote employees and contractors with access to your system.
- Access controls that restrict or limit the use of distracting websites and applications.
- Customizable alert systems that send reminders to employees who have been idle or distracted for too long.
Features for Data Security
If your organization needs to secure networks, drives, and devices, seek out UAM software that can:
- Block malicious activity and alert the security team to vulnerabilities with robust endpoint monitoring.
- Secure compromised devices using remote-wipe and lockout features.
- Seamlessly feed data to your SIEM with plug-and-play integration.
- Shut down attempted attacks before they succeed with alerts and automated responses.
Features for Ensuring Compliance
To maintain compliance with relevant industry regulations, choose UAM tools that allow your organization to:
- Implement internal controls to satisfy compliance requirements.
- Report on the presence and effectiveness of internal controls during compliance audits.
- Achieve compliance with major regulations using pre-built, out-of-the-box templates.
- Detect and intervene before non-compliance happens, minimizing penalties and fines.
- Inform forensic investigations with immutable activity logs, video recordings, and optical character recognition searches in the case of an incident.
Why is Teramind an Ideal Tool for Monitoring Employee Activity?
Try Teramind’s UAM solution → Take a self-guided product tour
Teramind offers a high-performance toolkit that includes real-time screen recording, keystroke logging, and Optical Character Recognition (OCR) to extract text from visual data.
Beyond standard monitoring, Teramind leads the industry with its AI agent governance feature; this allows businesses to audit AI prompts, distinguish human work from machine execution, and block unauthorized AI tools.
The platform balances robust security with employee trust via privacy-first deployment options, including customizable revealed or hidden agents. By utilizing smart rules and automated alerts, Teramind proactively prevents data breaches while ensuring compliance with global regulations like GDPR, HIPAA, and SOC 2.
FAQs
Which is the Best Overall Employee Monitoring Software?
Teramind is widely considered the best overall solution for organizations seeking a balance of security, productivity, and compliance.
It offers a comprehensive feature set including real-time session recordings, Shadow AI detection, and automated risk alerts, making it suitable for both small businesses and large enterprises.
How Do UAM Tools Help With Data Security?
UAM tools safeguard digital assets by providing insider threat detection and data loss prevention (DLP).
Key security features include:
- Automated Alerts: Instant notifications when sensitive data like SSNs is shared.
- Behavioral Analytics: Identifying risky user patterns before a breach occurs.
- Endpoint Control: The ability to block unauthorized USB devices or remotely lock down compromised endpoints.
- OCR Searching: Using Optical Character Recognition to find sensitive text within video screenshots.
Can User Activity Monitoring Improve Employee Productivity?
Yes. By providing visibility into active versus idle time, managers can identify workflow bottlenecks and optimize resource allocation.
Tools like ActivTrak and Insightful offer workforce analytics that monitor for signs of burnout, helping leaders understand productivity trends and prevent employee disengagement.
Is Employee Monitoring Software Legal and Private?
Most UAM tools are designed with privacy-first features to balance operational visibility with employee privacy rights.
Here are some examples:
- Privacy Controls: Some tools allow for the blurring of screenshots or exclude features like keystroke logging and camera access.
- Compliance: The most advanced UAM software provides pre-built policy templates, helping organizations meet global standards like the GDPR, HIPAA, and PCI DSS.
- Transparency: Many platforms offer visible monitoring modes for freelancers or remote teams.
How Much Do User Activity Monitoring Solutions Cost?
Pricing varies based on features and deployment models:
- Entry-level: Plans from providers like Hubstaff or Controlio can start as low as $4.99 to $6.67 per user per month.
- Mid-range: Professional suites with advanced security features typically range from $10 to $28 per user per month.
- Enterprise: Large-scale organizations often require bespoke pricing tailored to their specific infrastructure and professional service needs.
For more information, see Teramind’s guide to the cost of employee monitoring software.

