Teramind
in the News
Teramind leaders frequently provide analysis and opinion to media outlets on the most relevant Insider Risk and Workforce Management trends.
Press Releases are designed to keep our clients and followers informed of Teramind’s latest corporate developments, industry advancements, research, and major platform releases.
Press Releases
Latest Blog Posts
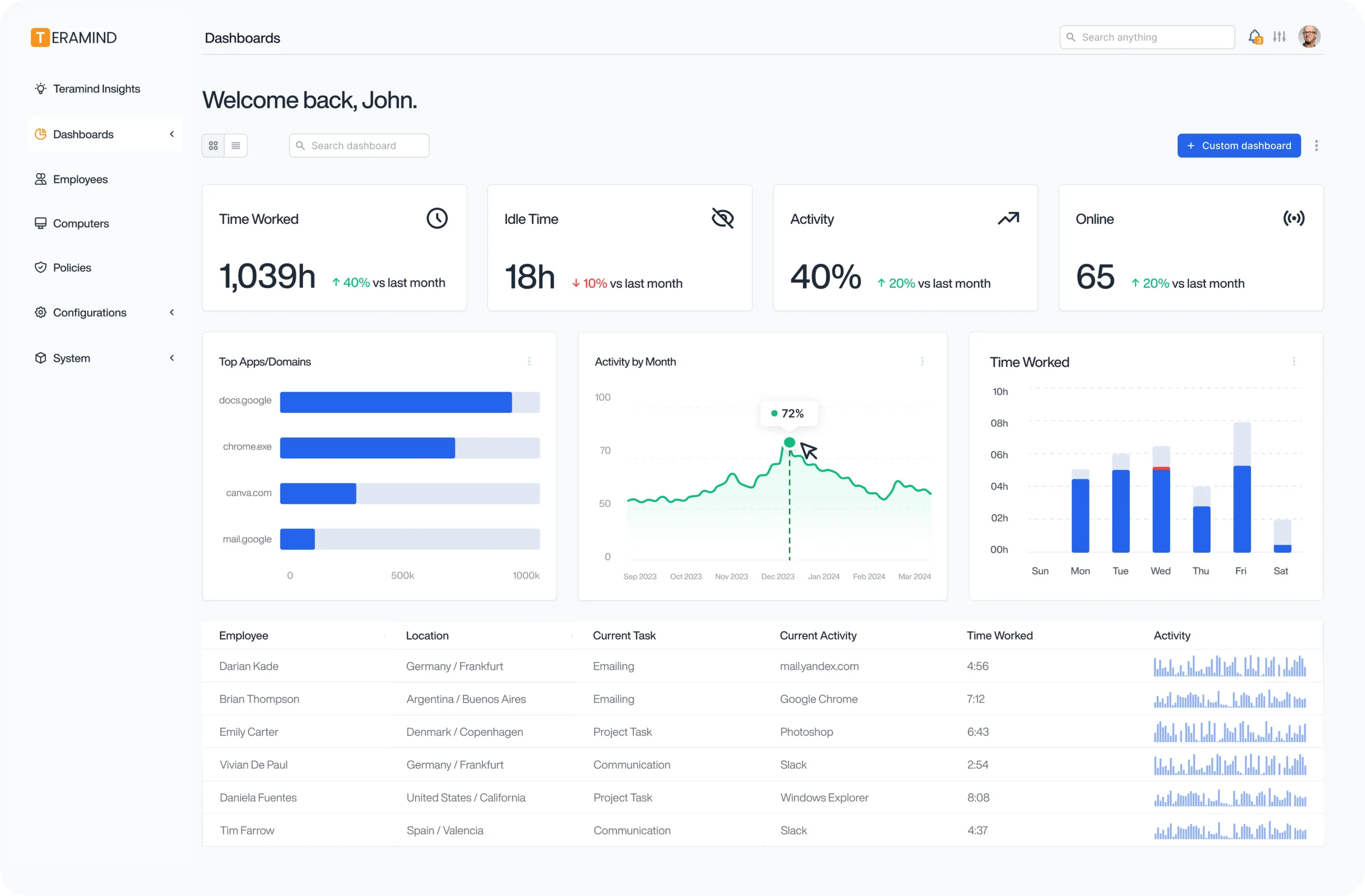
Try Platform
With a Live Demo
The Teramind Showcase
Interact with a live deployment of Teramind to see how it works.
On-demand walkthrough of our platform
What our Customers Say
“Convenient and comprehensive cloud based PC monitoring software. It’s easy to install, access and monitor client PCs. This is a mature and feature-rich solution for on-premise and remote user monitoring.”
Larissa H.
IT Support Specialist
“The best way and tools to supervise and control employees’ access to data, and their actions, ability to monitor and supervise employee activity with minimal manpower resources. These tools allow me to detect waste of time by employees and wasting company resources.”
Yakir D.
CIO
“Easy Implementation, Great UI, and amazing product. We leverage Teramind to manage high-risk situations to get in-depth visibility and alerting. It has far surpassed our expectations and has saved us significant data loss.”
IT Security & Risk Manager
$7B Manufacturing Enterprise
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics
4.6 out of 5 from 148 reviews
4.6 out of 5 from 86 reviews

4.8 out of 5 from 90 reviews