Power Your Decisions
With Teramind Insights
Starter
—
/seat /month
Total: — / monthSave 8%
(Billed monthly)
Best for basic productivity use cases & to identify risky users for investigation.
Quick and easy visual evidence capture and live playback, websites and apps tracking.
Package includes:
- Basic AI Governance
- Limited digital forensics & telemetry
- Limited behavior rules
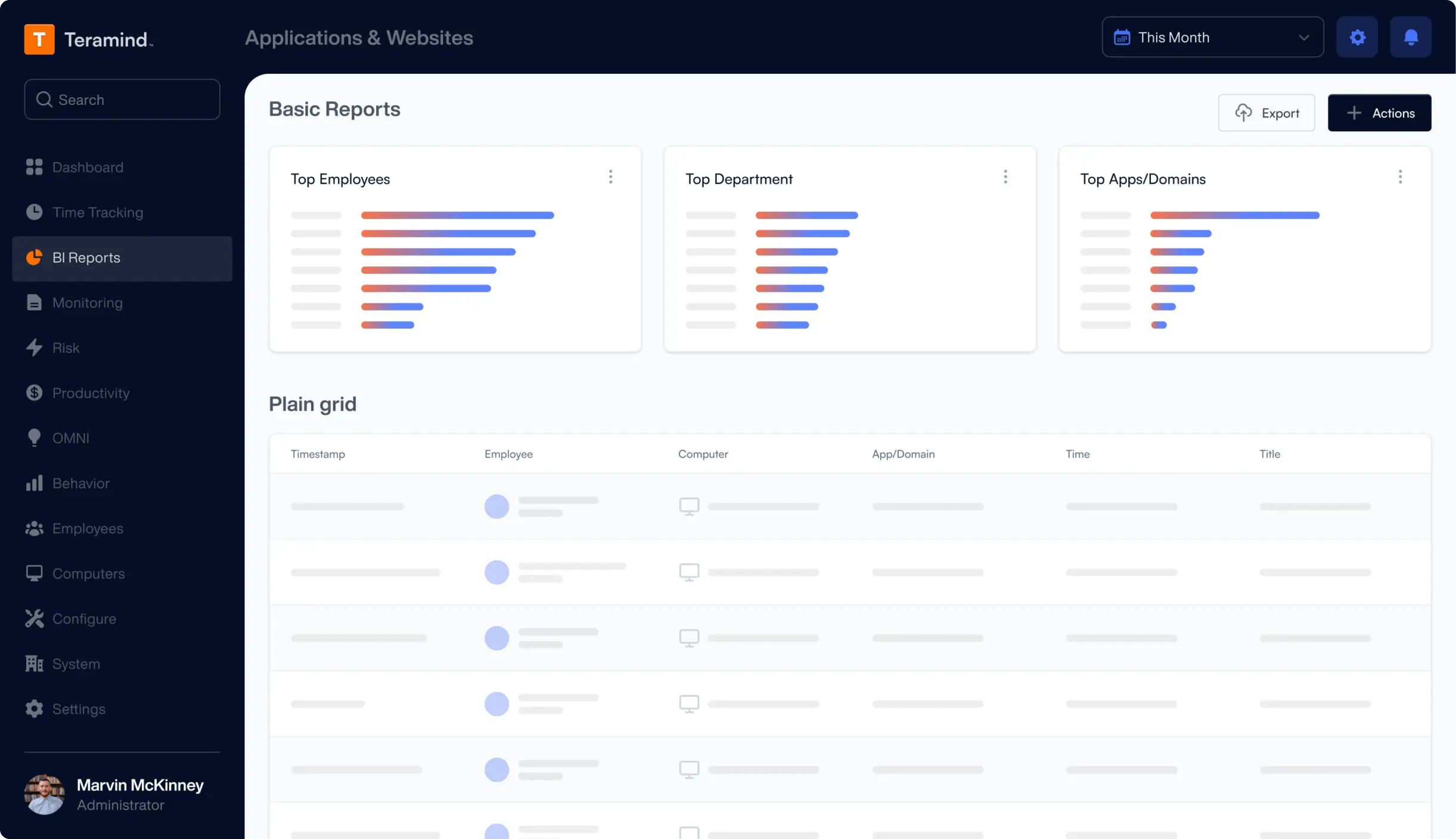
- Customizable BI dashboard
UAM
—
/seat /month
Total: — / monthSave 8%
(Billed monthly)
Best for comprehensive productivity optimization and security detection & investigation.
Digital activity & telemetry at its fullest: UEBA, audit, forensics, policies and rules.
Everything on Starter plus:
- LLM prompt/response recording
- Complete digital forensics & telemetry
- Unlimited activity-based behavior rules
- Pre-packaged productivity rules
- SIEM integration
- Keystroke logging
DLP
—
/seat /month
Total: — / monthSave 8%
(Billed monthly)
Complete security detection, automated response, data loss prevention, and forensic-grade activity monitoring-all in one platform.
Everything on UAM plus:
- LLM content rules
- Content-based behavior rules
- Sensitive content detection
- Redaction of sensitive content
- Malicious activity blocking
- 200 pre-packaged DLP rules
- Data protection rules
- Automatic DLP blocking
Enterprise
Custom
Contact salesBest rates
DLP & tailored professional services for the most demanding enterprises and government organizations.
Everything on DLP plus:
- In-app parsing for fraud detection & optimization
- Unlimited activity-based behavior rules
- OCR Engine
- Premium support & SLA
- Professional services & customizations
- AWS GovCloud & Azure Government availability
Compare benefits
User Activity Insights
Features
Starter
UAM
DLP
Enterprise
Screen recording / Live view
Remote control
OCR
Web pages & applications
Activity blocking
Console commands
File transfers
Instant messaging
Online Meetings
Social media activity
Keystrokes
Clipboard (copy and paste)
Searches
Printing
Camera Usage
Geolocation
Time tracking
Custom website field capture
Custom app field capture
Data Loss Prevention
Features
Starter
UAM
DLP
Enterprise
Protect all data types and IP
Content-based rules
File operation-based rules
Prevent malicious or negligent data exfiltration
Use pre-defined data discovery & classifications
Fingerprinting and tagging to protect sensitive data
Ensure compliance with GDPR, HIPAA, PCI DSS and more
In-app fraud detection
User Behavior Analytics
Features
Starter
UAM
DLP
Enterprise
Insider threat detection
Abusive & malicious behavior detection
Anomaly detection
Dynamic risk scoring
Productivity analysis & reporting
Template based scheduling
Policy and Rules Management
Features
Starter
UAM
DLP
Enterprise
Policy manager
Visual rule editor
Regular expression support
Out-of-the-box rule templates
Audit & Forensics
Features
Starter
UAM
DLP
Enterprise
Video and optional audio recording
OCR of screen content
Option to record only during rule violation
Full-text search
Professional Services
Features
Starter
UAM
DLP
Enterprise
Tailored deployment assistance
Custom reporting, behavior rules configuration, thirdparty integrations
Availability in AWS GovCloud and Azure Government
Enterprise SLA and premium support
Request Your
Custom Demo Now
An expert will walk you trough features
aligned to your use case.
- Customer Reviews
What our Customers Say
“The best way and tools to supervise and control employees’ access to data, and their actions, ability to monitor and supervise employee activity with minimal manpower resources. These tools allow me to detect waste of time by employees and wasting company resources.”
Yakir D.
CIO
“Easy Implementation, Great UI, and amazing product. We leverage Teramind to manage high-risk situations to get in-depth visibility and alerting. It has far surpassed our expectations and has saved us significant data loss.”
IT Security & Risk Manager
$7B Manufacturing Enterprise
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics
4.6 out of 5 from 148 reviews
4.6 out of 5 from 86 reviews

4.8 out of 5 from 90 reviews