User Behavior Advisory
Get help from seasoned human behavior experts.
Let experts show you which metrics are likely to matter most in your context, and how to interpret them.

The Process
Define which behaviors to track
Understand data and trends
Become an in-house expert
How we help
Define Key Performance Indicators
Interpret Data and Trends
Become an in-house expert
Teramind AI + Behavioral Data Advisory
With Teramind’s powerful new AI capabilities, your advisor can help you:
Uncover pods of internal toxicity.
organization using AI-powered relationship mapping & toxicity scoring.
Identify and interpret early signs of a threat.
organization using AI-powered relationship mapping & toxicity scoring.
Ensure 3 rd party contractors aren’t sharing credentials.
organization using AI-powered relationship mapping & toxicity scoring.
Detect worker activity falsification.
organization using AI-powered relationship mapping & toxicity scoring.
Key Data, Design, & Interpretation Capabilities
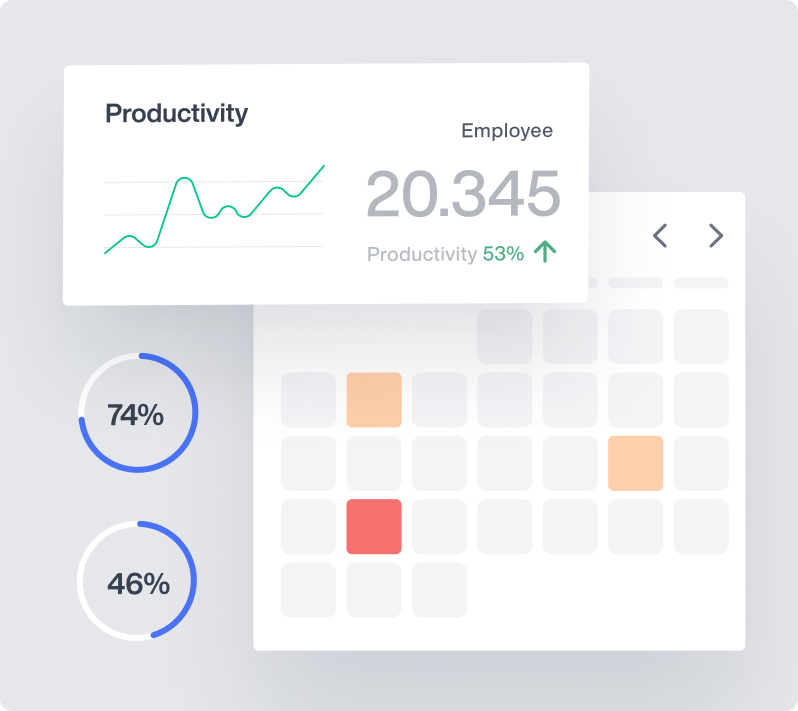
- Employee Productivity
- Business Process Optimization
- Fraud Identification
- Insider Risk Management
- Behavioral Data Loss
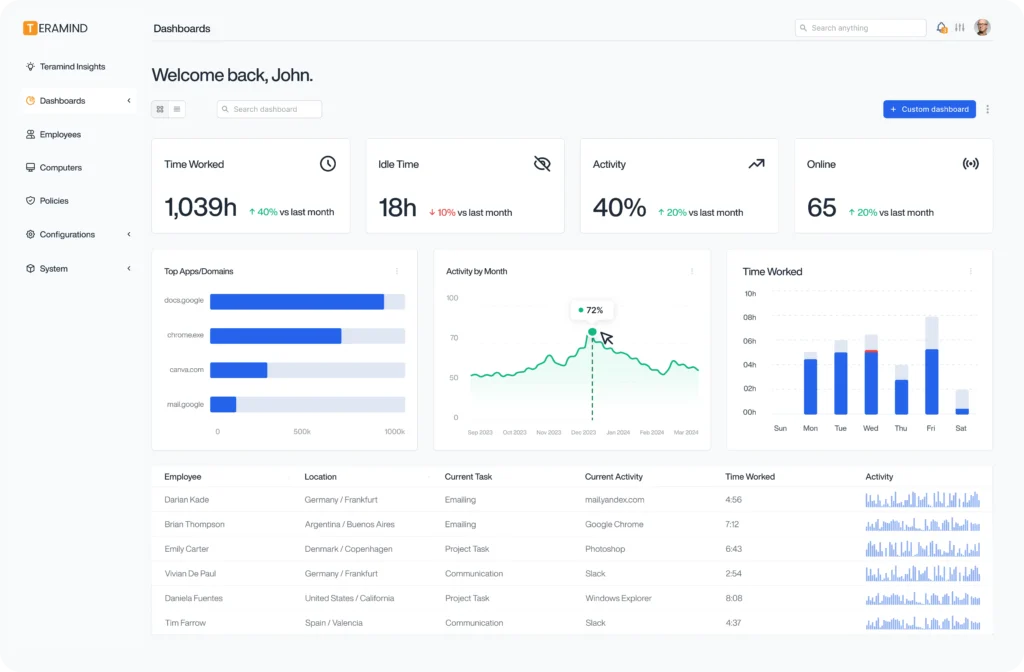
Try Platform
With a Live Demo
The Teramind Showcase
Interact with a live deployment of Teramind to see how it works.
On-demand walkthrough of our platform
Trusted by Leading Enterprises
Easy implementation, great UI, and an amazing product. We leverage Teramind to manage high-risk situations with in-depth visibility and real-time alerting. It has far surpassed our expectations and has saved us from significant data loss.

Convenient and comprehensive cloud-based PC management software. It’s easy to install, access, and gain visibility across client PCs. This is a mature and feature-rich solution for both on-premise and remote environments.
The best way and tools to manage and protect access to sensitive data, with strong visibility and control capabilities. The platform helps us safeguard company resources and improve operational efficiency with minimal manpower.

We were looking for a better way to protect sensitive financial data without overcomplicating our workflows. Teramind helped us tighten controls around data transfers and quickly spot unusual activity. It’s been especially helpful during compliance reviews, since we can easily pull the reports we need. Overall, it’s added an extra layer of confidence to our security program.
In healthcare, safeguarding patient information is a daily priority. Teramind has given us clearer visibility into how sensitive data moves across our systems, which has helped us strengthen our internal controls. The alerts are practical and easy to act on, and the reporting makes audit preparation much smoother. It’s been a valuable addition to our security toolkit.

We needed a solution that could support both our clinical and administrative environments without being overly complex. Teramind was straightforward to deploy and gave us better insight into potential risks across our endpoints. When questions come up, the investigation tools make it easy to review what happened and respond quickly. It’s helped us stay proactive instead of reactive.

Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics