Secure Insurance Data with Intelligent DLP
Safeguard protected health information (PHI), secure personally identifiable information (PII), and mitigate insider threats across your organization. Teramind delivers a data loss prevention experience built for the insurance industry, combining contextual analysis with robust protection to stop data loss incidents in real-time.
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics








Teramind for Insurance
Data breaches destroy trust. Secure patient data and critical data from unauthorized data transfers. Our DLP solution uses encryption and access restrictions to ensure data integrity across your data landscape.
Navigating data protection laws like the Health Insurance Portability and Accountability Act (HIPAA) is complex. Automate reporting capabilities and maintain tamper-proof logs to ensure compliance with data protection regulations.
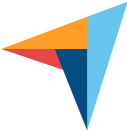
Malicious insiders seeking personal gain pose a severe risk. Detect unusual behaviors where users gain unauthorized access to proprietary data or attempt to steal sensitive data for competitors.
Intelligent Data Classification & Visibility
Legacy tools struggle to identify sensitive data amidst the noise. Teramind provides deep visibility into your data assets, helping you identify sensitive information like medical records and intellectual property. We help you implement a data loss prevention policy that distinguishes between legitimate work and data threats.
Automatically tag and classify sensitive data such as protected health information (PHI) and personally identifiable information. Apply data protection policies dynamically based on data sensitivity.
Enforce security measures that automatically encrypt data in motion. If a user attempts an unauthorized data transfer, Teramind blocks the action to protect confidential data.
Track data flows across cloud services and endpoints. Identify where critical data resides and ensure data protection requirements are met across the entire organization's data.
Insider Risk & Fraud Prevention
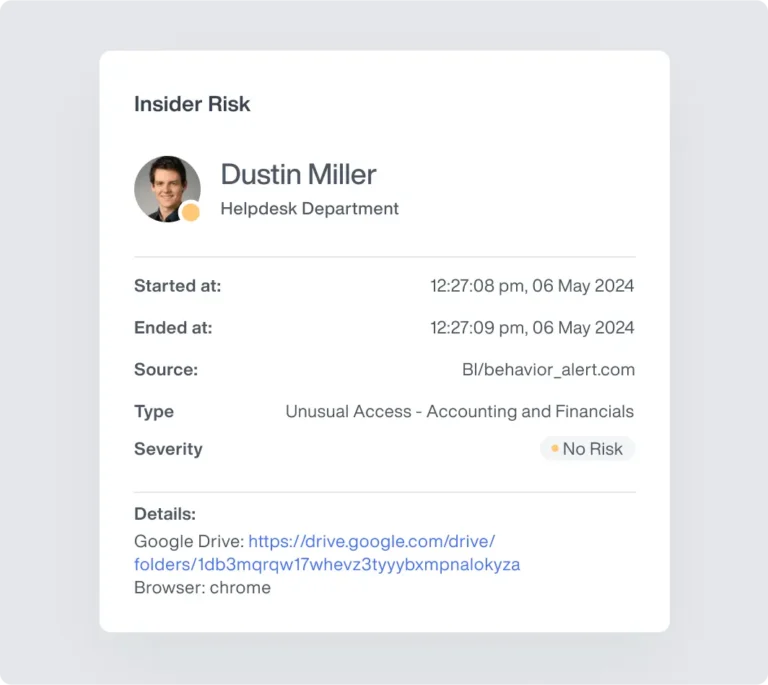
Inadequate security measures can lead to internal fraud. Teramind combines user behavior analytics with forensic screen recordings to spot insider threats—whether they are malicious insiders acting for personal gain or employees making errors.
Identify users attempting to gain access to sensitive information without authorization. Stop employees from stealing sensitive data or proprietary data before they leave the company.
Human error causes many data loss incidents. Automated pop-ups warn users if they try to send patient data to the wrong recipient, preventing accidental data loss.
Use screen recordings to investigate potential data breaches. See exactly why a security incident occurred, helping you refine your security strategy and mitigate insider threats.
Regulatory Compliance (HIPAA, CCPA, NAIC)
The insurance industry faces strict regulatory compliance demands. From HIPAA to the California Consumer Privacy Act (CCPA), Teramind provides the reporting capabilities and tamper-proof evidence needed to satisfy auditors.
Capture high-definition video of user screens during security alerts. See exactly what happened, how it happened, and who was involved.
View live desktop streams of high-risk users or remote teams to ensure protocols are being followed in real-time.
Keep a tamper-proof record of every keystroke, file movement, and application usage to support internal investigations and after-action reviews.

Full deployment within your own firewall or offline networks for maximum control and data sovereignty.
Dedicated cloud instances that ensure your data is never co-mingled.
Lightweight endpoint agents designed to operate silently without disrupting mission-critical applications or bandwidth.
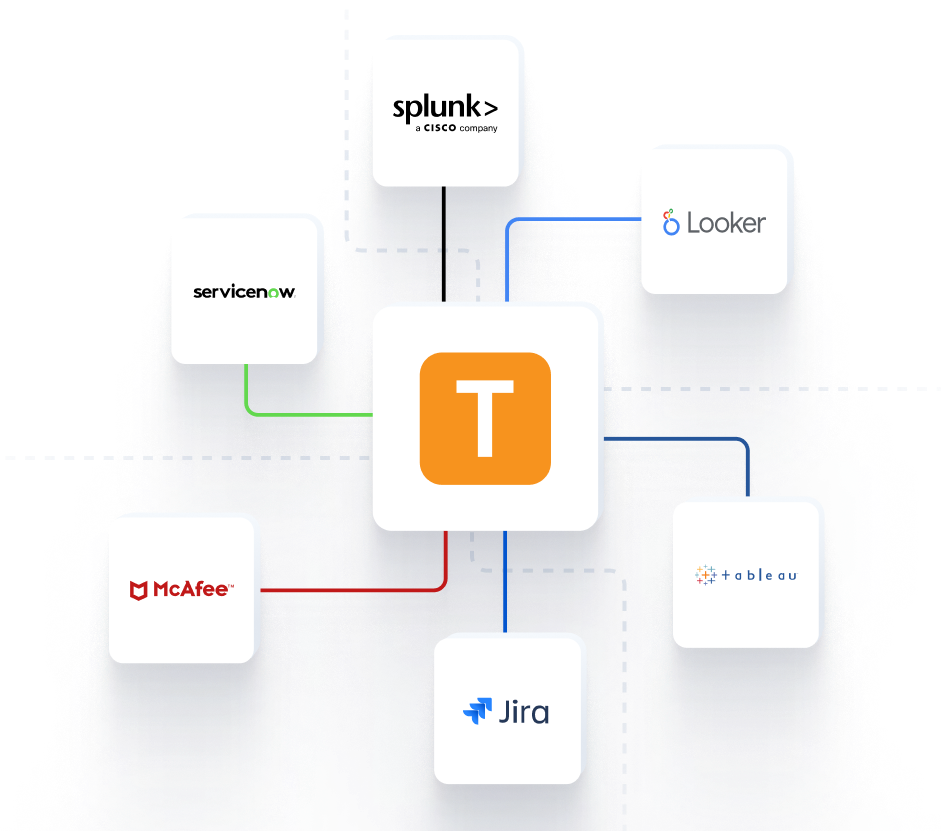
Seamless Integration into Your Command Center
Feed critical behavioral telemetry directly into your existing security infrastructure for a unified operational picture.



Teramind Success Stories
Arrivia Stopped an Insider Data Theft Ring with Teramind
Learn how a leading travel company used Teramind to improve productivity and ensure compliance with federal regulations while building legally defensible evidence for any violations.
FAQs
How does Teramind handle HIPAA compliance?
Teramind supports Health Insurance Portability and Accountability Act (HIPAA) compliance by monitoring access to protected health information (PHI). We provide tamper-proof audit trails and reporting capabilities to prove that security measures are in place to protect sensitive information.
What is the difference between malicious and accidental loss?
Human error (like emailing the wrong person) is accidental data loss. Malicious insiders act for personal gain to steal sensitive data. Teramind uses contextual analysis and screen recordings to distinguish between the two and apply the correct security policy.
How do you protect against insider threats?
We mitigate insider threats by analyzing user behavior. If an employee attempts to gain unauthorized access or transfer critical data to a personal drive, we block the action and alert your security team to the potential data breaches.
How do you secure field adjusters?
We provide endpoint protection for remote Windows, macOS, and Linux devices. This ensures continuous monitoring of data access and prevents unauthorized data transfers even when adjusters are working outside the corporate network, reducing data sprawl.
