Protect Patient Trust from the Inside Out
Stop healthcare data breaches before they start. Teramind delivers comprehensive insider risk management for the healthcare sector, combining human behavior analytics with security controls to detect insider threats, secure sensitive data, and protect patient records from malicious insiders and human error.
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics








Teramind for Healthcare
Healthcare is a prime target for financial gain. Detect malicious insiders selling patient data on the black market or stealing billing information. Analyze user activity to spot suspicious behavior before it leads to financial impact.
Employees often have more access than necessary. Enforce access controls and manage access requests to critical systems. Prevent users from attempting to escalate privileges or gain access to sensitive protected health information.
Negligent insiders cause more security issues than hackers. Reduce accidental exposure of sensitive patient information by identifying security weaknesses in employee behavior. Address human error with real-time alerts that reinforce security policies.
Avoid non-compliance penalties. Maintain a tamper-proof audit trail of all access to medical devices and patient information. Automate regular audits to prove your risk management strategy meets strict HIPAA compliance standards.
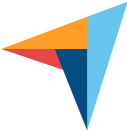
Identify & Assess Insider Risks
Insider risk in healthcare organizations is complex. Teramind provides the visibility needed to uncover blind spots in your attack surface. We help security teams analyze behavioral indicators to identify potential risks from employees, contractors, and third party vendors.
Track user activity across electronic health records (EHR) systems. Identify users who access patient records without a valid patient care reason, flagging potential snooping.
Detect anomalies like bulk exports of sensitive data or off-hours access requests. Immediate visibility allows you to take immediate action against suspicious activity.
Use screen recordings to investigate security threats. See exactly what happened during an incident, distinguishing between accidental exposure and malicious intent.
Protect Sensitive Patient Data
Patient data commands a high price on the black market. Teramind secures personal health information and billing information from data breaches. We help you implement access management policies that restrict access to sensitive patient data based on risk level.
Stop insider threats from transferring vast amounts of healthcare data to external drives or cloud storage. Protect patient data from leaving the secure healthcare environment.
Monitor interaction with connected workstations. Ensure security controls are active and sensitive information isn't exposed to external threats.
Enforce multi-factor authentication and access controls dynamically. If risk scores rise, automatically revoke access to sensitive patient information to prevent identity theft.
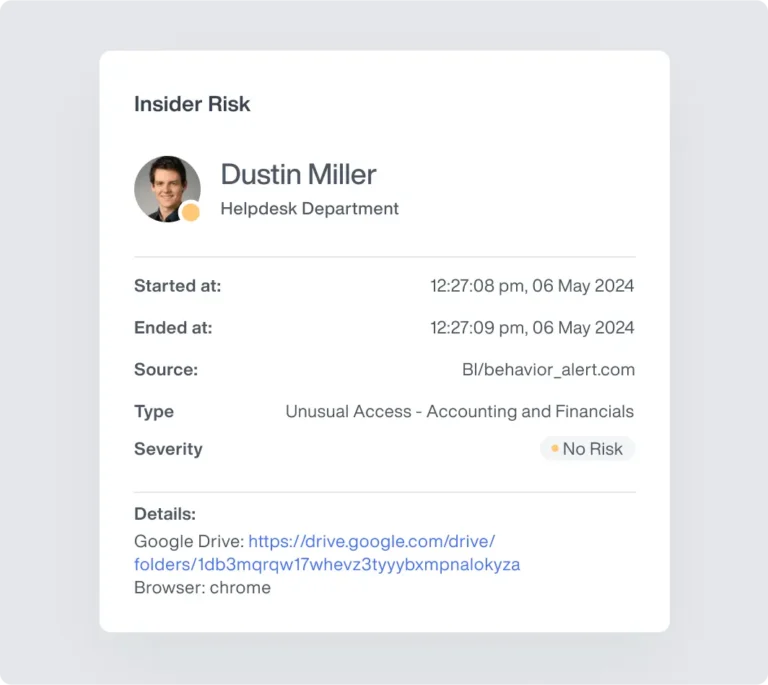
Unmatched Forensic Visibility
Capture high-definition video of user screens during security alerts. See exactly what happened, how it happened, and who was involved.
View live desktop streams of high-risk users or remote teams to ensure protocols are being followed in real-time.
Keep a tamper-proof record of every keystroke, file movement, and application usage to support internal investigations and after-action reviews.

Automated Compliance & Governance
Regulatory compliance is non-negotiable. Teramind automates the evidence collection for HIPAA compliance and other healthcare industry mandates. We provide the audit trail and risk assessments needed to prove access governance and data protection.
Generate tamper-proof logs of every access event. Prove to auditors that you have control over protected health information and sensitive patient information.
Monitor third-party vendors with access to your systems. Ensure their security controls align with your internal standards to prevent supply chain data breaches.
Accelerate incident response with detailed forensics. Quickly determine the scope of potential threats and demonstrate due diligence in mitigating insider risk.
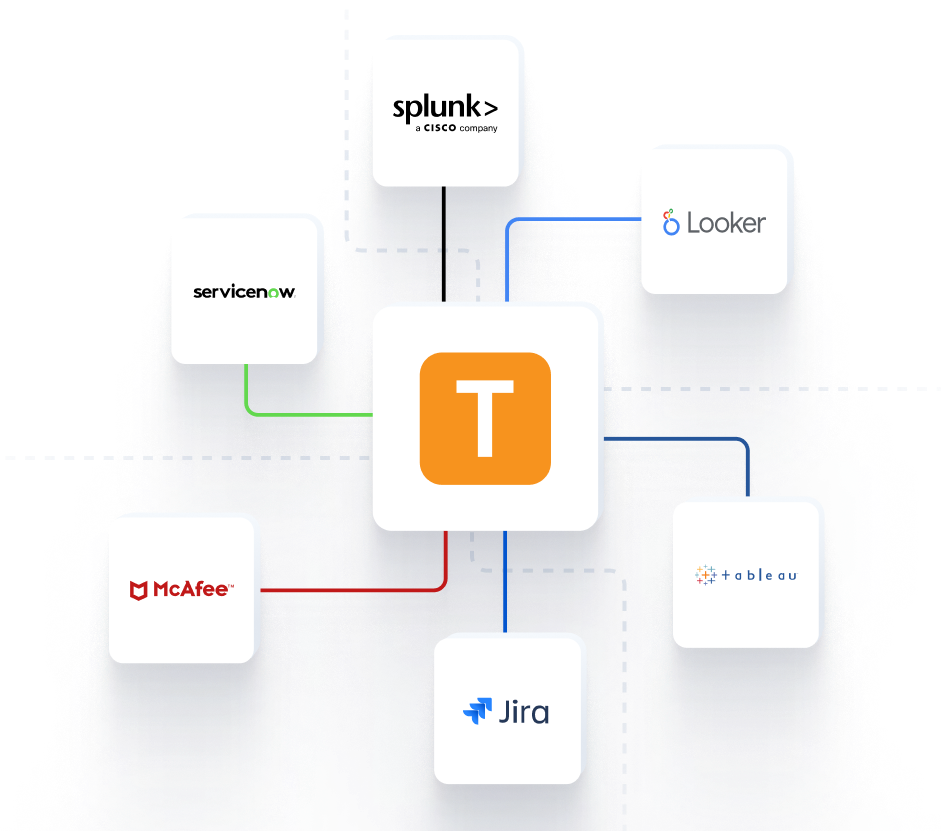
Seamless Integration into Your Command Center
Feed critical behavioral telemetry directly into your existing security infrastructure for a unified operational picture.



Teramind Success Stories
Arrivia Stopped an Insider Data Theft Ring with Teramind
Learn how a leading travel company used Teramind to improve productivity and ensure compliance with federal regulations while building legally defensible evidence for any violations.
FAQs
How does Teramind distinguish between patient care and snooping?
We analyze context. By correlating user activity with patient care schedules and access requests, we can flag suspicious behavior—like a nurse accessing the patient records of a VIP or neighbor—that falls outside standard workflows.
Can you detect data theft for the black market?
Yes. Financial gain is a key motivator for malicious insiders. We detect vast amounts of billing information or sensitive patient data being exported or copied, enabling security teams to intervene before it reaches the black market.
Does this help with HIPAA compliance?
Absolutely. We provide the audit trail, access controls, and risk assessments required for HIPAA compliance. Our platform helps healthcare organizations prove they are actively managing insider risk and protecting protected health information.
How do you handle negligent insiders?
Human error is common. We focus on education. When negligent insiders attempt to send sensitive information via unsecure channels, we block the action and notify them, preventing accidental exposure without punitive measures.
Do you monitor third-party vendors?
Yes. Third-party vendors often have access to sensitive systems. We visualize their activity just as we do for internal employees, ensuring they don’t introduce security risks or weaknesses into your environment.
Is the platform compatible with medical devices?
We monitor the workstations and servers that interface with medical devices. This ensures critical systems remain secure and patient data generated by these devices is protected from insider threats.
How does this protect patient trust?
Patient trust relies on privacy. By preventing healthcare data breaches and identity theft, you demonstrate a commitment to security. Stay ahead of potential threats to ensure patient information remains confidential and secure.
