Stop Insider Threats Before Financial Harm Occurs
Protect your institution from data theft, fraud detection failures, and compliance violations. Teramind delivers insider risk management for banks and financial institutions, combining user behavior analytics with forensic screen recordings to neutralize insider risks in real-time.
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics








Teramind for Insider Risks
Insider incidents often lead to financial gain or money laundering. Detect suspicious activity and fraudulent accounts instantly to stop financial crime and protect business operations.
Privileged accounts hold the keys to critical systems. Monitor authorized access to legacy systems and infrastructure security agency assets to prevent sabotage systems or malicious software deployment.
Your intellectual property and algorithms are targets for malicious insiders. Stop intellectual property theft and data breaches by identifying data movement patterns that signal the theft of sensitive information.
Avoid regulatory penalties and significant harm to your reputation. Automate internal controls for the Bank Secrecy Act and data protection regulations with tamper-proof evidence.
Detect & Stop Malicious Insiders
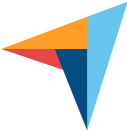
Logs alone cannot distinguish between a mistake and malicious intent. Teramind provides the deeper understanding needed to identify disgruntled employees or compromised insiders. By pairing user behavior analytics with forensic screen recordings, you can determine if an insider threat incident is imminent.
Identify unusual behaviors that precede data theft, such as access data attempts on sensitive systems or hoarding customer data before resignation.
Detect intentional threats where users attempt to sabotage systems or delete financial records. Our prevention systems lock down endpoints instantly.
Ask Timmy to analyze historical data to find potential threats. Quickly uncover if an employee is colluding with external threat actors or a foreign government.
Secure Privileged & Legacy Access
Privileged access to legacy systems is a top vector for insider risks. Teramind monitors privileged accounts with granular visibility, ensuring legitimate access isn’t abused for financial gain or workplace violence (digital sabotage).
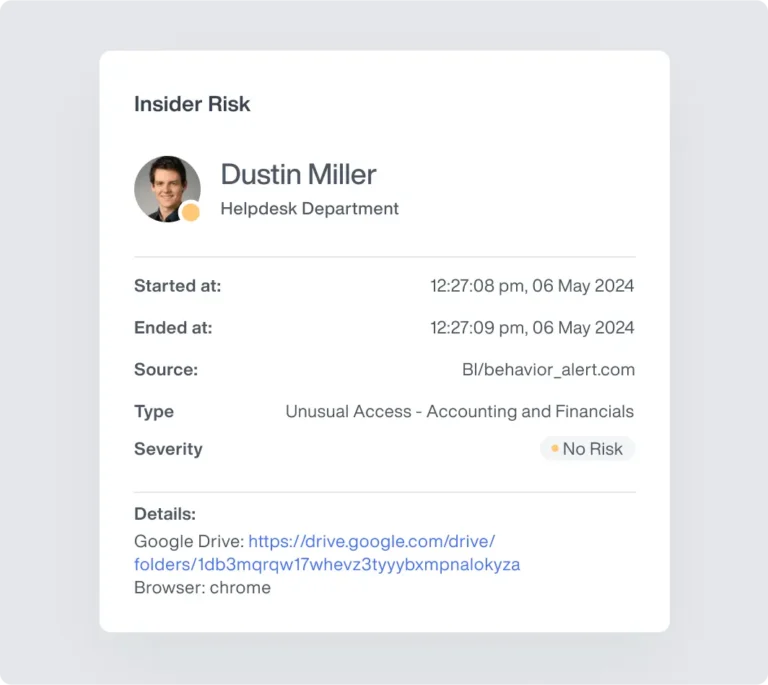
Record every session on critical systems and financial services infrastructure. If privileged access is misused, you have immediate, irrefutable video evidence.
Prevent data exfiltration via external devices (USBs) or personal devices. Ensure sensitive information never leaves the financial sector environment.
Monitor vendors and contractors who have authorized access. Ensure their insider risk controls match your internal security protocols.
Mitigate Negligence & Human Error
Not all insider threats are malicious; many are negligent insiders. Teramind helps you reduce business risk caused by human error, such as sending sensitive data to the wrong recipient or falling for phishing attacks.
Stop accidental data loss by blocking emails containing personally identifiable information (PII) or trade secrets sent to public domains.
Trigger automated warnings when users violate security protocols. This "just-in-time" training helps prevent insider threats without involving human resources.
Mitigate the risk of lost or stolen devices. Teramind’s endpoint protection ensures sensitive information remains encrypted and inaccessible to external threats.

Forensics & Compliance Readiness
Regulatory compliance in the financial services industry demands more than just checkboxes. Teramind provides tamper-proof logs and workforce visibility to prove your insider threat program meets federal law enforcement and Bank Secrecy Act standards.
Maintain tamper-proof logs of all user behavior and insider incidents. Defend against compliance violations with evidence that stands up to scrutiny.
Use screen recordings to investigate security breaches fast. See exactly what malicious insiders did, reducing the time to resolution for insider risk management.
Dynamically adjust access to sensitive systems based on risk scores. If escalating threat levels are detected, the system automatically revokes legitimate access.
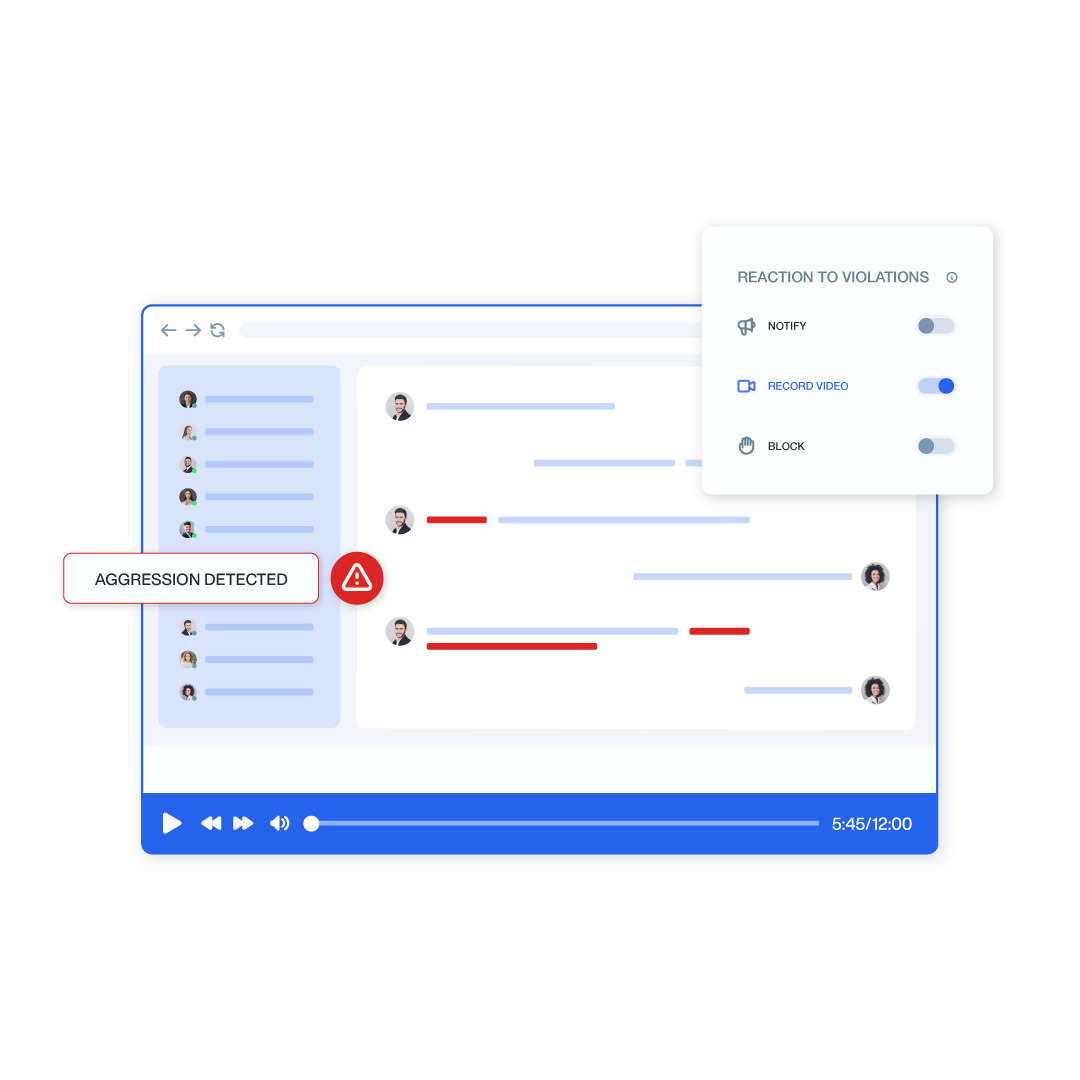
Seamless Integration into Your Command Center
Feed critical behavioral telemetry directly into your existing infrastructure for a unified operational picture.



Teramind Success Stories
Arrivia Stopped an Insider Data Theft Ring with Teramind
Learn how a leading travel company used Teramind to improve productivity and ensure compliance with federal regulations while building legally defensible evidence for any violations.
FAQs
How does Teramind differentiate between negligence and malicious intent?
Determining malicious intent requires context. Teramind combines user behavior analytics with screen recordings. This allows you to see why an action occurred—whether it was negligent insiders making a mistake or malicious insiders stealing sensitive information for financial gain.
Does this solution help with the Bank Secrecy Act (BSA)?
Yes. Teramind supports Bank Secrecy Act compliance by monitoring suspicious activity and ensuring internal controls are effective. Our tamper-proof audit trails provide the evidence needed for regulatory compliance and financial crime investigations.
How do you handle privileged access users?
Privileged accounts pose a significant business risk. We record 100% of sessions for users with privileged access to critical systems. This ensures legitimate access isn’t abused and provides a deeper understanding of all admin activities.
Is this effective against external threat actors?
While our focus is insider risk banking, Teramind detects external threats that compromise insider credentials. By identifying unusual behaviors (like impossible travel or phishing attacks), we stop compromised insiders before significant harm occurs.
How does this fit into our existing insider threat program?
Teramind acts as the “eyes” of your insider threat program. We integrate with SIEMs and HR systems to correlate human resources data (like disgruntled employees) with digital risk management indicators, helping you mitigate insider threats holistically.
