Comprehensive Security for Autonomous AI Agents
Protect sensitive information with an AI agent security solution that delivers complete visibility into agent behavior. Equip security teams with continuous monitoring and audit trails to prevent data exfiltration and stop compromised agents before they execute unintended actions.
Trusted by 10,000+ organizations to improve productivity, security, compliance, and workforce analytics








The Pillars of Agent Security
Track how autonomous AI agents operate on your endpoints to detect rogue agents and shadow AI installations. We use anomaly detection to identify superhuman command execution, giving you complete visibility into agent activity.
Stop autonomous agents from causing malicious data leaks or data exfiltration. Implement data protection rules that block agents from accessing confidential data or copying sensitive data into external data sources.
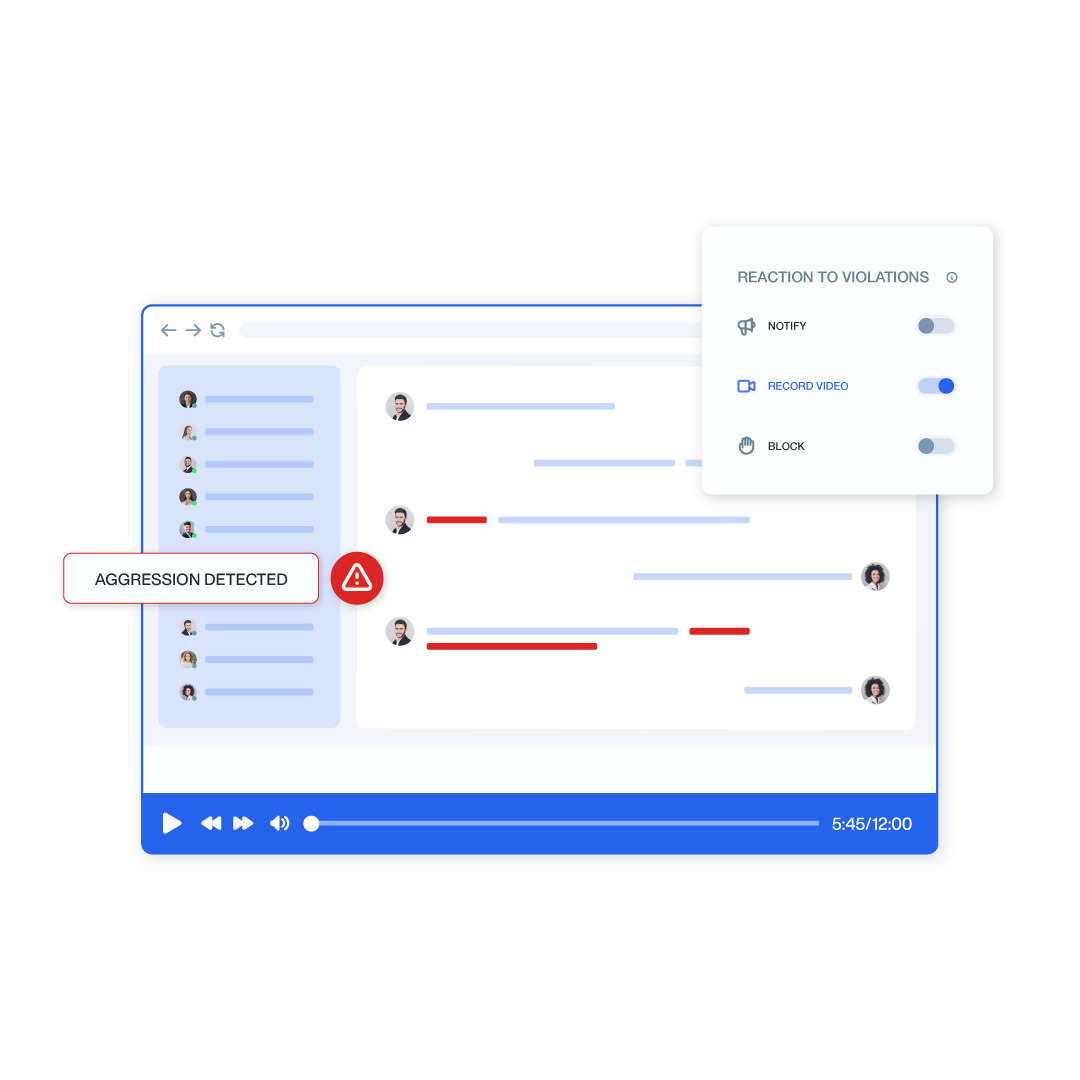
Ensure human in the loop workflows by recording the exact moments when users interact with AI systems. Capture prompt injection attempts and track when employees accept malicious instructions from compromised agents.
Adopt a zero trust architecture for your machine learning systems by blocking unauthorized agents. Our security posture relies on network drivers to stop agents that attempt to bypass your business logic or access paths.
Visibility into Autonomous AI Systems
As organizations begin deploying agents, they introduce entities that can read files, execute code, and browse the web. Teramind acts as the black box recorder for agentic AI systems, offering unparalleled visibility into how these tools function.
Use screen recordings and Optical Character Recognition to capture the suggestions AI agents create and the subsequent actions taken by users.
Log all keystrokes to maintain audit trails of the prompts fed to AI agents, helping you identify indirect prompt injection and data poisoning attempts.
When agents act as a surfing assistant, our platform logs every URL change and web event just as if a human user were navigating the cloud environments.
Stop Rogue Agents and Shadow IT
Security teams face major challenges when employees install unauthorized, open-source multi agent systems. Teramind provides runtime protection by identifying compromised agents through their behavioral footprint.
Detect rogue agents by their impossible speed, flagging extreme command line activity when a process fires hundreds of times in seconds.
Stop unauthorized agents from communicating by monitoring default gateway ports and WebSocket handshakes, effectively neutralizing supply chain attacks.
Identify when an agent attempts privilege escalation or unauthorized lateral movement by tracking the creation of temporary configuration files and memory databases.
Secure Agent Tools and Console Workflows
Terminal-based agents operate directly within your command line, presenting unique security gaps. We monitor these agent tools to ensure they do not execute malicious instructions or modify critical business logic.
Capture the back-end commands executed through processes like PowerShell, providing a transcript of all agent actions and tool calls.
Gain visibility into file access patterns to see exactly which multiple data types and project files the AI systems modified during a session.
Create rules based on window titles to increase recording frequency when specific agent identities or terminal workflows become active on a machine.

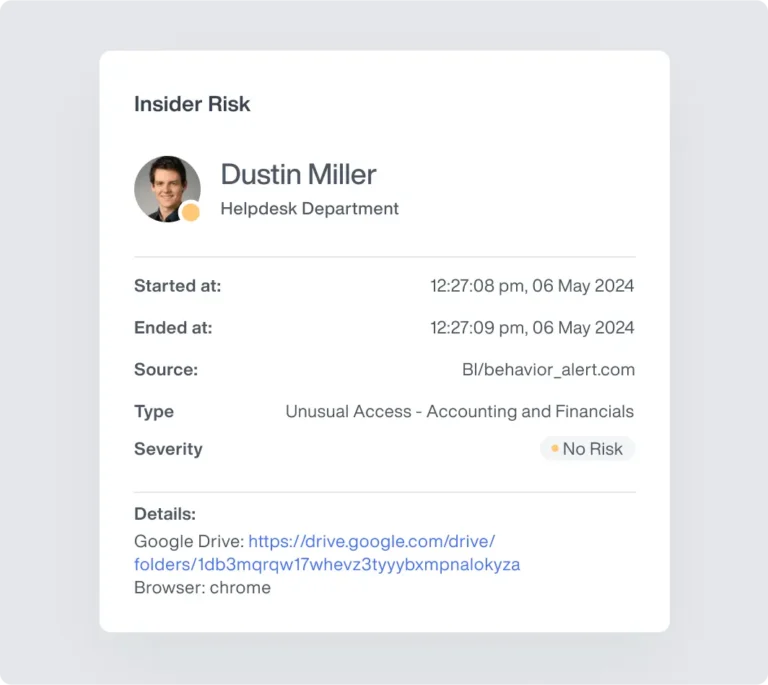
Continuous Monitoring and Data Protection
Secure AI requires enforcing your existing security best practices across all autonomous systems. Teramind ensures that AI agents are subject to the same strict data protection rules as human employees.
Monitor clipboard activity to track the movement of sensitive information from AI interfaces into corporate documents, stopping data exposure.
Rely on our network drivers and certificate inspection to block agents that behave like an unauthorized proxy, providing robust runtime behavior defense.
Ensure that your established blocking rules still work, preventing an agent's access from bypassing URL filters to reach restricted HR portals or sensitive repositories.
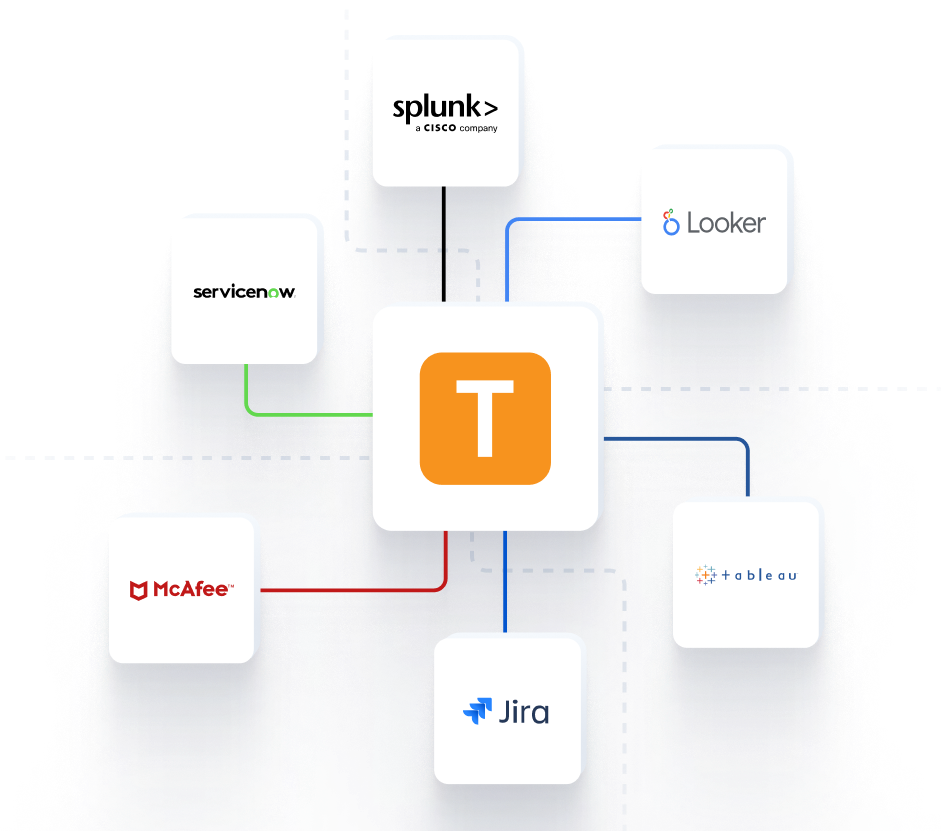
Seamless Integration into Your Command Center
Feed critical behavioral telemetry directly into your existing security infrastructure for a unified operational picture.



Teramind Success Stories
Arrivia Stopped an Insider Data Theft Ring with Teramind
Learn how a leading travel company used Teramind to improve productivity and ensure compliance with federal regulations while building legally defensible evidence for any violations.
FAQs
How does Teramind secure AI agents on the endpoint?
Our AI agent security solution uses a combination of screen recording, keystroke logging, and OCR to monitor agent behavior. This ensures you have continuous monitoring over what the AI systems see and do.
Can Teramind detect prompt injection attacks?
By capturing the exact prompts users input and the outputs generated by the autonomous AI agents, security teams can audit sessions to identify hidden instructions or injection patterns.
How does Teramind protect sensitive data from agents?
We enforce data protection by monitoring clipboard activity and applying URL filtering. This prevents agents from copying confidential data into external data sources or unauthorized models.
What happens if rogue agents are deployed?
We use behavior analytics to detect superhuman execution speeds and monitor specific network ports. This identifies rogue agents and shadow AI tools even if users rename the execution files.
Do you monitor terminal and command line agents?
Yes. We capture console command logging to provide a full transcript of the commands executed by terminal agents, ensuring they do not perform unauthorized tool calls or lateral movement.
Does Teramind support human in the loop security?
Absolutely. We track the human-AI collaboration process, auditing when a human reviews, copies, or accepts data generated by AI agents to ensure proper human oversight.
How does Teramind fit into a zero trust architecture?
Our solution aligns with zero trust principles by constantly verifying agent activity. We use certificate inspection and network drivers to block autonomous agents that lack proper security handshakes, maintaining your trust architecture.
