Protecting Our Platform: How Teramind Is Responding to the Misuse of Our Software by Threat Actors
Earlier last month, security researchers published two detailed reports documenting how cybercriminals built fake Zoom and Google Meet websites to trick people into downloading software onto their machines without their knowledge. Threat actors obtained a Teramind trial installer and distributed a modified version of it without Teramind’s authorization or involvement.
No systems compromised. No customer data accessed or affected.
New security measures across provisioning, distribution, and access.
Continue to trust Teramind for compliance and security.
What happened
The facts
Threat actors created convincing phishing sites that impersonated Zoom and Google Meet. Visitors were shown what appeared to be a live video call with connection issues. After a few seconds, a fake “update” prompt appeared, and a renamed Teramind installer file was automatically downloaded to the visitor’s machine. Installation could then occur if the user executed the downloaded file and approved the installer prompt.
Our systems were not breached. Our infrastructure was not compromised. The activity involved third parties obtaining a trial installer and distributing it without Teramind’s authorization as part of a phishing campaign. While this misuse did not involve any compromise of our platform, we recognize that software bearing our name was distributed in a way that could mislead users, and we take that seriously. Teramind software is designed for lawful enterprise compliance monitoring and security purposes. Any distribution or deployment of the software outside of authorized enterprise use is something we don’t agree with and violates our Terms of Service.
Immediate response
What we did immediately
Containment
Every known Teramind instance identified in connection with these attacks has been shut down.
Investigation
Prevention
No new trial accounts can generate installers without additional verification.
Architecture
Multiple new security measures being implemented to prevent future misuse.
What we're changing
Comprehensive platform hardening
We have stopped all automated free trial provisioning while we implement stronger fraud prevention checks. Previously, a bad actor could sign up for a free trial and immediately generate a fully functional agent installer. That pathway is now closed. New trial access will require additional verification before any agent can be deployed.
We are improving our KYC program to require more stringent identity verification before granting full platform access. Our goal is straightforward: make it significantly harder for anonymous bad actors to obtain a working Teramind deployment while keeping the process practical for the legitimate businesses we serve.
In addition to our forced MFA already in place we are integrating an IP reputation API to screen all connections to the Teramind dashboard. Access attempts originating from VPNs, proxies, Tor exit nodes, and other anonymizing services will be blocked. Threat actors rely on these services to obscure their identity when setting up and managing fraudulent instances. Removing that cover makes it harder to operate on our platform without leaving a traceable footprint, and it complements the KYC checks by adding a real-time technical layer to our identity verification efforts.
We need to be direct about this, because it featured prominently in the reporting. Teramind offers a deployment option called Hidden Agent, commonly referred to as stealth mode. In its intended context, this is a legitimate and widely used enterprise feature. Organizations deploy our agents in hidden mode for insider threat detection, compliance monitoring, and security investigations. This occurs on company-owned devices, with appropriate legal authorization and employee notice policies in place.
In this campaign, threat actors exploited that capability to install our agent on personal devices without the victim’s knowledge. This represents an intentional misuse of the feature outside its intended enterprise context and our Terms of Service. We are implementing additional safeguards around how the feature is provisioned.
Stealth mode restrictions are a critical change
Going forward, stealth mode will not be available on any authorized Teramind accounts, trial or paid, without going through our extended KYC process. Trial deployments will operate in revealed installer mode only, meaning the agent’s presence will be visible to the user of the device during installation.
This ensures no silent installs on trial accounts.
If someone tries to trick a victim into running the installer, the victim sees exactly what’s being installed before anything happens.
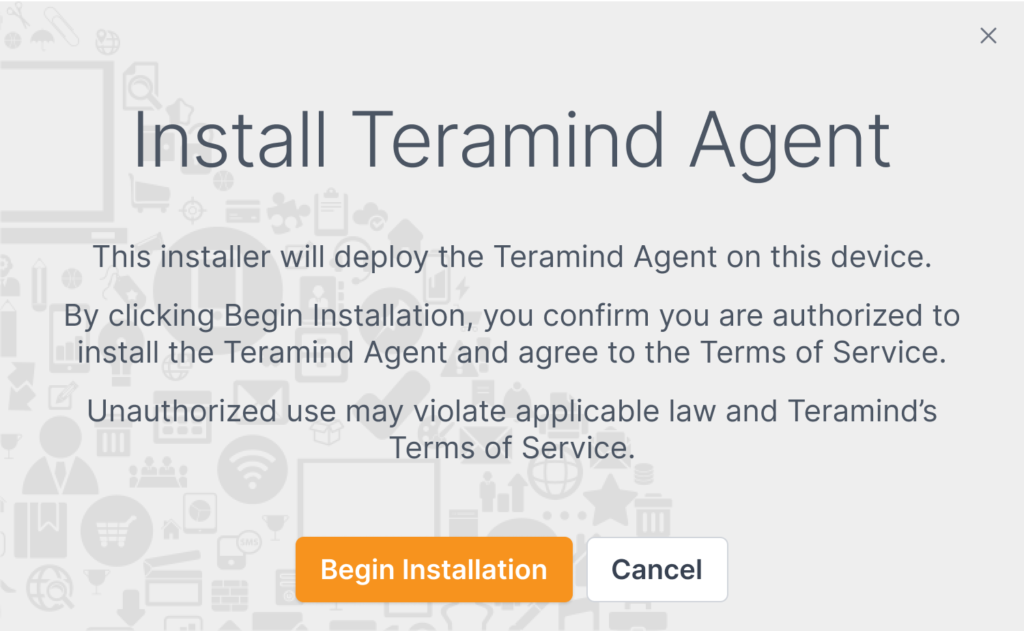
This is what the new installation popup looks like. The installer clearly identifies itself as Teramind, explains what it does, confirms the user is authorized, and warns that unauthorized use may violate the law. Trial deployments now operate in this revealed installer mode only.
The reported deep dive documented how a single binary could serve multiple attacker accounts because the installer reads its configuration from its own filename. Attackers exploited this by renaming the file to include their account identifier, disguising it as a Zoom or Google Meet component.
We are enforcing a fixed filename structure for installation files so that the installer name can no longer be arbitrarily changed. This removes the ability for a threat actor to rebrand the file to impersonate other software.
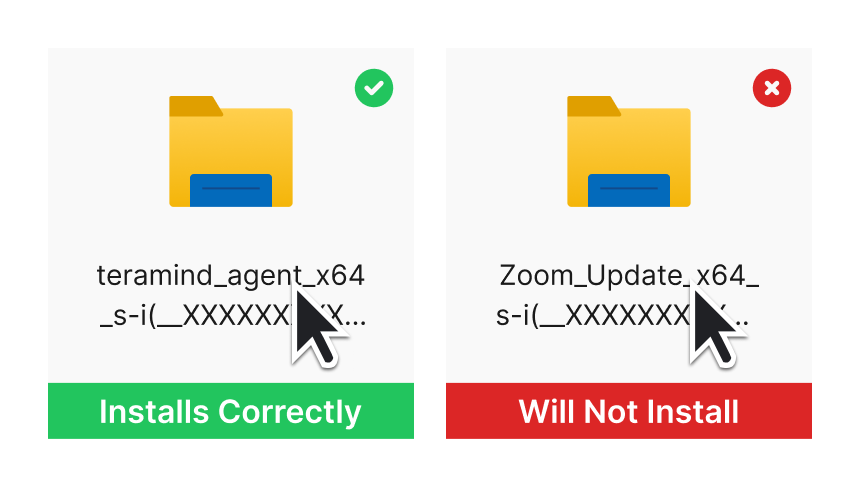
The installer now validates its own filename before running. A legitimate Teramind agent installs normally. But if someone renames the file to impersonate Zoom, Google Meet, or anything else, the installation simply refuses to proceed.
One of the technical changes we want to highlight addresses the potential mechanisms that may have made malicious attacks scalable. As the analysis detailed, a single installer binary could be pointed at any number of attacker-controlled accounts by intentionally and maliciously modifying the base Teramind code and changing the filename or overriding configuration properties at install time.
To address this, we are implementing additional controls so that agents can verify they are communicating only with the Teramind instance for which they were generated. For example, implementing certificate pinning so that each agent is cryptographically bound to a specific Teramind instance. If a threat actor attempts to redirect the agent to a different server, the connection will fail.
This significantly reduces the ability to redirect installed agents to unrelated instances.
Free trial accounts will now be limited to a maximum of five connected agents unless a Proof of Value agreement is in place. This constraint is designed to make our trial useful for legitimate evaluation purposes while sharply reducing its value as a tool for broad surveillance campaigns.
We have deployed new algorithms and enhanced our detection capabilities specifically designed to improve our detection of fraudulent instances across our cloud deployments. Our fraud team is actively checking for patterns consistent with misuse. This includes anomalous signup behavior, unusual agent deployment patterns, and connections from infrastructure associated with known malicious activity. Instances identified as potentially abusive are being shut down proactively.
This is an ongoing effort that will continue to be improved upon as new threat vectors emerge.
What we shipped
All safeguards at a glance
Here’s the full list. Some are already live, others are rolling out as we finalize the engineering work.
No automated trial provisioning. Additional verification required before agent deployment.
More stringent identity verification before granting full platform access.
VPN, Tor, and proxy connections to dashboard blocked via IP reputation API.
Hidden agent requires extended KYC. Trials operate in revealed installer mode only.
Installer name enforced and validated. No more impersonation via rename.
Each agent cryptographically bound to one tenant. One agent, one instance.
Anomalous signups and deployments detected and terminated proactively.
Dedicated reporting channel for anyone who believes Teramind is being misused.
Industry context
A broader problem, and our responsibility within it
The misuse of legitimate commercial software by threat actors is not unique to Teramind. It is a growing pattern across the enterprise software industry. Remote access tools, IT management platforms, and behavior telemetry solutions have all been co-opted by attackers precisely because they are trusted, professionally built, and designed to operate reliably.
If malicious actors modify our services beyond their intended and authorized purpose, if someone is harmed by software that carries our name, we will take action. We will investigate and take steps consistent with our Terms of Service and security policies.
We are examining how malicious actors exploit our platform and will continue to make structural changes that reduce the likelihood of it happening again. For clarity, the specific accounts involved have been shut down. Addressing those accounts was the initial step. The additional precautionary safeguards described above, designed to further strengthen controls, reflect our ongoing efforts to operate our platform responsibly and continue earning the trust organizations place in Teramind.
Going Forward
Our commitment
Teramind is used by thousands of organizations around the world for lawful insider threat protection, compliance monitoring, and workforce productivity management. That trust is something we have tirelessly worked to earn over years, and it is something we intend to protect.
Teramind does not authorize the installation of its software on devices without appropriate authorization from the device owner or administrator and in compliance with applicable laws and organizational policies.
We will continue to be transparent about this situation as our response evolves. If you are an existing customer with questions about these changes, please reach out to your account team. If you are a security researcher with information related to this or similar campaigns, we welcome your outreach through our Report Misuse page so we can work with you directly.
We have always been a company that demonstrates instead of talks. We look forward to showing everyone what we ship and what we stand for.
Isaac Kohen, CIO at Teramind
Whether you’re a customer, a researcher, or someone who believes Teramind is being misused, we want to hear from you.
